1. What are the 5 Information security levels?
The information security level framework is a government-issued classification system designed to determine the importance of each information system and establish the corresponding protection requirements. The more critical a system and the more sensitive the data it processes, the higher the security standard it must meet.
This framework is formally governed by two core documents: Decree 85/2016/ND-CP (issued on July 1, 2016) and Circular 12/2022/TT-BTTTT (effective October 2022). Decree 85 establishes the criteria for determining each level, while Circular 12 provides detailed implementation guidance and specific technical requirements per level. This classification is also a critical component of legally compliant digital transformation for Vietnamese businesses.
The five levels are structured around a core principle: the higher the level, the more critical the system is to state operations, the economy, or national security, and the more stringent the protection requirements. Level 1 applies to the simplest internal systems; Level 5 is reserved for systems of the highest national importance.
Any organization operating an information system in Vietnam, including private businesses providing online services, falls within the scope of this regulation. Failure to comply can result in administrative fines, mandatory remediation, or service suspension.
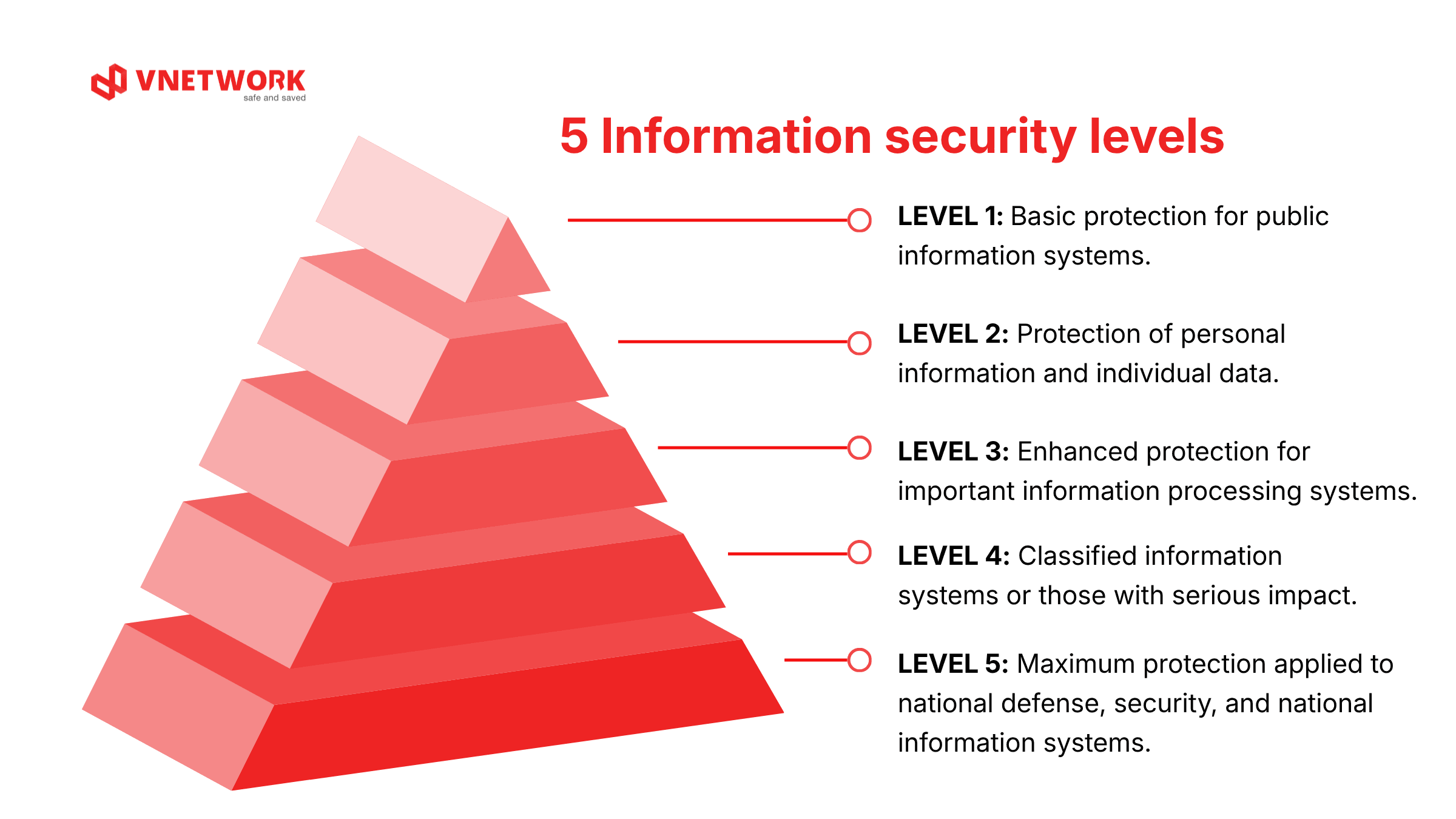
2. Detailed classification of each level
Level 1: Simple internal systems
Per Article 7 of Decree 85/2016, this is the lowest level, applicable to systems that serve only the internal operations of an organization and handle only public information — meaning information that does not require user identity verification to view.
Real-world examples: Company introduction websites with no login functionality, advertising landing pages, internal notice boards, and offline attendance management software with no internet connectivity.
Level 2: Systems with small-scale private data
Per Article 8 of Decree 85/2016, Level 2 applies when a system handles private information or personal data of users but at a limited scale. Specifically, this covers online services with fewer than 10,000 users, or online services that do not fall under the category of conditional business services.
Real-world examples: Newly launched online stores, restaurant table-booking apps, recruitment websites with account registration forms, and SME CRM software.
Level 3: The critical threshold many businesses overlook
Per Article 9 of Decree 85/2016, a system falls under Level 3 when any of the following criteria are met:
- Provides online services that process private or personal data for 10,000 or more users.
- Provides online services in a conditional business sector.
- Is shared IT infrastructure serving multiple agencies or organizations within a single industry or province.
- Processes state secrets or supports national defense and security in a way that, if disrupted, would cause harm to national defense or security.
Real-world examples: Large e-commerce platforms, digital wallets, digital banking apps, private hospitals with online patient management systems, large-scale online learning platforms, insurance companies with online customer portals, and peer-to-peer lending fintech companies.
This is the level that many technology companies, fintech firms, digital health platforms, and online education providers can fall into without realizing it, especially when their user base exceeds the 10,000-account threshold.
Level 4: Critical national systems
Per Article 10 of Decree 85/2016, Level 4 is designated for systems with a significant impact on e-Government operations or critical national IT infrastructure, with mandatory 24/7 uptime and no tolerance for unplanned downtime.
Real-world examples: The national public services portal, the interbank payment system, and nationwide shared IT infrastructure. These systems are typically managed by government agencies and fall outside the scope of most private businesses.
Level 5: Systems of the highest national importance
Per Article 11 of Decree 85/2016, this is the highest level, applicable to systems where an attack or disruption would cause especially serious harm to national security. The list of Level 5 systems is approved by the Prime Minister.
Real-world examples: National defense and security systems, and Vietnam's international internet gateway infrastructure. This level is entirely outside the scope of private businesses.
3. Comparison of the 5 information security levels
| Criteria | Level 1 | Level 2 | Level 3 | Level 4 | Level 5 |
|---|---|---|---|---|---|
| Type of information processed | Public information | Private, personal data (under 10,000 users) | Private data at scale (10,000+ users) or state secrets | State secrets; serious impact on national defense and security | State secrets; especially serious impact on national security |
| Typical business type | Company intro websites, internal notice boards, offline attendance software | Small online stores, restaurant booking apps, SME CRM | Large e-commerce platforms, digital wallets, digital banking apps, private hospitals, online learning platforms, fintech | National e-Government portal, interbank payment systems, nationwide shared IT infrastructure | National defense, national security systems, international internet gateway infrastructure |
| 24/7 operation required | No | No | Not mandatory | Mandatory | Mandatory |
| Assessment body | Internal (dedicated unit) | Internal (dedicated unit) | MICT leads (max 15 working days) | MICT + inter-ministry (max 30 working days); competent authority approves level | Prime Minister approves list |
| Required technical level | Basic | Intermediate | High | Very high | Maximum |
4. How to determine your information security level
To correctly determine the applicable level based on the criteria in Articles 7 to 11 of Decree 85/2016, business owners need to clarify four key points:
What type of information does the system process?
Clearly distinguish between public information (accessible to anyone without authentication) and private information (requiring identity verification). Does the system process personal data such as full names, phone numbers, addresses, or transaction histories? If it does, the system has already moved beyond Level 1.
How many users does the system serve?
This is the single most important threshold for private businesses, per Articles 8 and 9 of Decree 85/2016. Systems serving fewer than 10,000 active users fall under Level 2. Systems serving 10,000 or more are classified as Level 3 and are subject to significantly higher requirements.
Does the service operate in a conditional business sector?
Finance, banking, insurance, healthcare, pharmaceuticals, and online education are all conditional business sectors. If a business provides online services in any of these fields, the system must meet at least Level 3 under Article 9 of Decree 85/2016, regardless of the number of users.
Does the system require continuous operation?
If the system must operate around the clock with no tolerance for unplanned outages, this is a characteristic of Level 4 under Article 10 of Decree 85/2016. These systems are typically part of e-Government infrastructure or critical national IT infrastructure.
Important note (Article 5 of Decree 85/2016): When a system comprises multiple subsystems of different levels, the overall classification is determined by the highest level among those subsystems.

5. Technical and management requirements by level
Each level imposes two categories of requirements: management and technical. These requirements are detailed in the five annexes of Circular 12/2022 and reference the TCVN 11930:2017 standard.
Management requirements (applicable from Level 1, increasing by level)
Per Annexes I to V of Circular 12/2022, management requirements are organized into seven groups, applied on a cumulative basis:
- Establish a written information security policy, reviewed and updated on a regular schedule (all levels).
- Establish or designate a dedicated information security unit (all levels).
- Manage information security personnel throughout their entire employment lifecycle (all levels).
- Manage information security incidents; manage end-user security (from Level 2 onward).
- Manage information security vulnerabilities; manage system security monitoring; implement systematic anti-malware management (from Level 3 onward).
- Maintain a risk management plan and a decommissioning and disposal plan for the system (all levels).
Technical requirements: Minimum network segmentation
Per Annexes I to V of Circular 12/2022, the minimum number of required network zones increases by level:
- Level 1: Internal network zone, edge network zone, and DMZ.
- Level 2: Adds an internal server zone; wireless network zone (if present) must be isolated.
- Level 3: Adds a database server zone and an administrative zone.
- Level 4 & 5: Adds a separate system device management zone.
Level-specific technical requirements (excerpted from Circular 12/2022 annexes)
- Level 1: Must implement a plan for access management and secure remote system administration using a VPN or equivalent; a plan for controlling access between network zones and intrusion prevention using a firewall with integrated intrusion prevention functionality; and a malware protection plan for servers and workstations.
- Level 2 (in addition to Level 1): Must implement a web application attack prevention plan using a web application firewall (WAF) for systems with web applications; an email security plan; and a redundancy plan for core network devices including the central switch and central firewall.
- Level 3 (in addition to Level 2): Must implement a load balancing and hot standby plan for core network devices; a database server security plan using a database firewall; a malware filtering plan for the network environment using a firewall with integrated anti-malware functionality; a denial-of-service attack prevention plan using enterprise services or dedicated hardware; a centralized information security monitoring plan using a SIEM product; a network-layer access control plan; and a data loss prevention plan for systems processing state secrets.
- Level 4 (in addition to Level 3): Must implement a privileged account management plan using a PAM (Privileged Access Management) product; and a centralized system monitoring plan using a dedicated centralized monitoring platform.
- Level 5 (in addition to Level 4): Must implement a geographically separated backup system plan with a minimum distance of 30 km between sites; and a network connection redundancy plan between primary and backup systems.
6. Implementation process: From documentation to approval
Once the level has been determined, the organization follows the process set out in Chapter III of Decree 85/2016 and Chapter II of Circular 12/2022:
Step 1: Prepare the level proposal dossier (Article 15 of Decree 85/2016)
The dossier consists of four main components: a system overview document; a construction design or preliminary design document; a document explaining the rationale for the proposed level based on legal criteria; and a document presenting the information security plan for the corresponding level.
Step 2: Assessment and approval (Articles 12, 16, and 17 of Decree 85/2016)
- Levels 1 and 2: Assessed and approved internally by the organization's own dedicated information security unit.
- Level 3: Led by the Ministry of Information and Communications (MICT), with a maximum processing time of 15 working days.
- Levels 4 and 5: Inter-ministry coordination is required, with a maximum assessment period of 30 working days.
- Dossier approval processing time: maximum 7 working days after receipt of a complete and valid submission.
Step 3: Implement the approved security plan
After the dossier is approved, the business must fully implement the approved security plan before putting the system into operation. For systems already in operation, existing measures must be reviewed and any gaps must be addressed. From Level 3 onward, many technical requirements demand advanced expertise, including the deployment of WAF, DDoS protection, centralized monitoring systems, and ransomware defenses.
Step 4: Periodic inspection and assessment (Article 20 of Decree 85/2016)
- Levels 3 and 4: Annual information security inspection and assessment.
- Level 5: Inspection every six months, or ad hoc when necessary.
- All levels: Comprehensive assessment every two years.
- Level 3 and above: Inspections must be conducted by a licensed professional organization.
Step 5: Periodic reporting (Articles 13 and 14 of Circular 12/2022)
Each year, the operating unit submits a report to the system owner by December 20. The system owner consolidates and submits the report to MICT by December 25 of the same year.

7. Legal risks and consequences of non-compliance
Failure to correctly classify a system's level or to implement the corresponding security plan is not merely an administrative violation — it also leaves serious security gaps. A data breach resulting from an inadequately protected system can cause far greater damage than the initial cost of compliance.
Direct legal risks
- Administrative fines under cybersecurity law.
- Mandatory full remediation within a specified deadline.
- Unannounced inspections by competent state authorities.
- In serious cases, the organization may be required to suspend service delivery until all requirements are met.
Real-world security risks
- Absence of a web application firewall exposes the system to exploitation via vulnerabilities such as SQL injection and XSS.
- Lack of a DDoS protection solution makes services vulnerable to disruption.
- Absence of backup and recovery mechanisms leads to complete data loss in the event of a ransomware attack or hardware failure.
- Lack of centralized monitoring means the organization cannot detect sophisticated attacks such as zero-day exploits until it is too late.
8. Conclusion
The 5-level information security framework is not an administrative burden — it is a substantive protection structure that helps businesses operate more securely as cyber threats grow increasingly complex. The first and most important step is correctly identifying the level of the systems currently in operation. From there, organizations will know what needs to be done, where to focus efforts, and who to work with.
For systems at Level 3 and above, VNETWORK provides a complete set of technical solutions that meet the requirements of Circular 12/2022, including web application security (VNIS), DDoS protection, email security (EG-Platform), and cloud infrastructure (VCLOUD). Contact VNETWORK for guidance on determining your system's level and a deployment roadmap suited to your business scale.
9. Disclaimer and references
This article has been prepared for the purpose of providing general information about Vietnam's information security level classification framework. The content does not constitute formal legal advice. Applicable regulations may be amended or supplemented over time. To accurately determine a system's level and implement the appropriate information security plan for a specific system, organizations should consult the original legal texts directly and/or engage a licensed professional advisory firm.
- Decree No. 85/2016/ND-CP dated July 1, 2016 of the Government on ensuring information system security by level: Link
- Circular No. 12/2022/TT-BTTTT dated August 12, 2022 of the Minister of Information and Communications detailing and guiding the implementation of certain articles of Decree 85/2016/ND-CP: Link
- Law on Cybersecurity No. 86/2015/QH13 dated November 19, 2015: Link
- National Standard TCVN 11930:2017 on Information Technology — Security Techniques — Basic requirements for information system security by level: Link
FAQ — Frequently asked questions about information system security levels
1. Are private businesses required to comply with the 5-level information security regulation?
Yes. Under Article 2 of Decree 85/2016/ND-CP, this regulation applies to all organizations and individuals involved in building, operating, or managing information systems in Vietnam, including private businesses providing online services, applications that process personal data, or IT infrastructure serving multiple organizations.
2. Does the information security level need to be updated when the system changes?
Yes. Under Article 18 of Decree 85/2016, when a system is significantly expanded, upgraded, or changed in scope, scale, or type of data processed, the system owner must review the level proposal dossier and adjust the security plan accordingly. The re-classification process follows the same sequence as the initial determination.
3. What is the main difference between Level 3 and Level 4?
Level 3 (Article 9 of Decree 85/2016) applies to systems processing state secrets or online services serving 10,000 or more users. Level 4 (Article 10) is designated for more critical national systems and adds mandatory 24/7 uptime requirements, hot standby redundancy for core network devices, privileged account management, and a dedicated system device administrative zone.
4. Can a business be penalized if it has not yet prepared a level proposal dossier?
Yes, administrative fines may be imposed under cybersecurity law. In addition to fines, the business may face the risk of being required to suspend service delivery or perform full remediation within a specified deadline.
5. What should a business do first to start complying with the regulation?
The first step is to correctly identify the type of information system in operation per Article 6 of Decree 85/2016, then cross-reference the criteria in Articles 7 to 11 to determine the applicable level. The next steps are to prepare the level proposal dossier, organize the assessment, and implement the corresponding security plan. For Level 3 and above, working with a licensed professional advisory organization is strongly recommended.