Why do businesses need professional DDoS protection in 2025?
DDoS attacks are growing more sophisticated and automated
DDoS attacks are no longer just about flooding a system with traffic. Attackers now deploy AI-generated botnets, multi-vector attacks, and Layer 7 bypass techniques to defeat conventional defenses. In Vietnam, financial platforms, e-wallets, stock trading systems, and e-commerce sites are frequent targets.
Attackers often combine UDP-based volumetric floods with TCP-layer request attacks, sending over 2,500,000 simultaneous requests while continuously rotating IPs to evade detection. By 2025, the number of DDoS attacks is projected to double compared to 2023 in both scale and frequency.
Direct and indirect financial impact
- Direct revenue loss from service unavailability during downtime.
- Recovery costs: engaging specialists, upgrading infrastructure, emergency software procurement.
- Brand damage and loss of customer trust, with consequences that often persist for months after an incident.
For a mid-sized business in Vietnam, each minute of downtime can mean millions to tens of millions of VND in lost revenue. For financial services and e-commerce, the figure can be exponentially higher.
DDoS as a "smokescreen" for secondary threats
Many attackers use DDoS as a distraction. While the system scrambles to handle abnormal traffic, they quietly exploit vulnerabilities to steal data, deploy ransomware, or seize system control. This is why DDoS protection is not just about maintaining uptime — it is the first line of defense for the entire security infrastructure.

Why do businesses need professional DDoS protection in 2025?
DDoS attacks are growing more sophisticated and automated
DDoS attacks are no longer just about flooding a system with traffic. Attackers now deploy AI-generated botnets, multi-vector attacks, and Layer 7 bypass techniques to defeat conventional defenses. In Vietnam, financial platforms, e-wallets, stock trading systems, and e-commerce sites are frequent targets.
Attackers often combine UDP-based volumetric floods with TCP-layer request attacks, sending over 2,500,000 simultaneous requests while continuously rotating IPs to evade detection. By 2025, the number of DDoS attacks is projected to double compared to 2023 in both scale and frequency.
Direct and indirect financial impact
- Direct revenue loss from service unavailability during downtime.
- Recovery costs: engaging specialists, upgrading infrastructure, emergency software procurement.
- Brand damage and loss of customer trust, with consequences that often persist for months after an incident.
For a mid-sized business in Vietnam, each minute of downtime can mean millions to tens of millions of VND in lost revenue. For financial services and e-commerce, the figure can be exponentially higher.
DDoS as a "smokescreen" for secondary threats
Many attackers use DDoS as a distraction. While the system scrambles to handle abnormal traffic, they quietly exploit vulnerabilities to steal data, deploy ransomware, or seize system control. This is why DDoS protection is not just about maintaining uptime — it is the first line of defense for the entire security infrastructure.
Criteria for selecting the best DDoS protection service in 2025
Attack processing bandwidth (Tbps)
Tbps is the most critical metric for a system's capacity to absorb attacks. A large-scale volumetric attack can reach hundreds of Gbps or even several Tbps. If the protection system cannot handle the load, the entire website goes down in seconds. Businesses should prioritize providers with a capacity of 10 Tbps or more, backed by distributed scrubbing mechanisms to prevent bottlenecks.
Protection layers: Layer 3/4/7
DDoS attacks can target multiple layers of the OSI model. The three most commonly exploited layers are:
- Layer 3 (Network): ICMP flood, IP spoofing — targeting the network layer.
- Layer 4 (Transport): SYN flood, UDP flood — exhausting connection resources.
- Layer 7 (Application): HTTP GET/POST flood — the most sophisticated, mimicking legitimate user behavior to bypass standard defenses.
A service that only protects one layer is insufficient. Layer 7 is typically the weakest point, requiring intelligent WAF and behavioral analysis to distinguish real traffic from attack traffic.
WAF, CDN, AI/ML, and SOC 24/7 ecosystem
WAF (Web Application Firewall) protects web applications by blocking SQL injection, XSS, and HTTP flood attacks. CDN distributes traffic globally to reduce load on the origin server. AI/ML identifies new attack patterns in real time. A 24/7 SOC ensures human experts are available to intervene in complex situations that automated systems cannot handle alone.

SLA and uptime commitment
The SLA reflects the provider's commitment to performance. Prioritize providers offering attack mitigation within 10 seconds, uptime of ≥99.9%, and clear compensation policies when commitments are not met.
Quick comparison: top 9 DDoS protection services in 2026
| Provider | Key strengths | Best suited for |
| VNIS VNETWORK | All-in-one: DDoS mitigation, AI WAF, Multi-CDN 2,300+ PoPs, Vietnamese-language SOC 24/7. Processing capacity: 2,600 Tbps. | Vietnamese businesses, SME to Enterprise, requiring fast local support |
| Cloudflare | Global distributed network, integrated CDN and WAF, free tier available for basic protection | Global businesses needing broad CDN coverage and a rich ecosystem |
| Imperva | Specialized in protecting both web applications and databases, with a global scrubbing center network | Finance, e-commerce, organizations with database protection requirements |
| Radware | Deep expertise in Private/Public Cloud infrastructure, highly flexible and customizable | Telcos, large cloud providers, complex infrastructure environments |
| Akamai | Comprehensive enterprise security ecosystem combining professional SOC with an intelligent platform | Large global enterprises requiring enterprise-grade security infrastructure |
| AWS Shield | Natively integrated into the AWS ecosystem, with Standard (free) and Advanced (paid) tiers | Businesses already running systems on AWS |
| Sucuri | Lightweight solution combining WAF, CDN, and IDS; cost-effective for SME budgets | Small and medium websites with budget-conscious requirements |
| Netscout | Specialized in mobile network and telecom infrastructure protection, supports on-premise deployment | ISPs, telcos, businesses requiring on-premise control |
| Link11 | AI-driven automatic traffic filtering, fast onboarding, 24/7 support from Europe | Businesses operating in Europe or requiring compliance with EU security standards |
Top 9 DDoS protection services in 2026
1. VNIS VNETWORK — All-in-one platform, purpose-built for the Vietnamese market
As Vietnamese businesses face a growing wave of DDoS attacks targeting financial platforms, stock trading systems, and e-commerce, VNIS, developed by VNETWORK, stands out as the all-in-one security platform specifically engineered to meet these challenges, with strong domestic infrastructure, 24/7 Vietnamese-language support, and processing capacity of up to 2,600 Tbps.
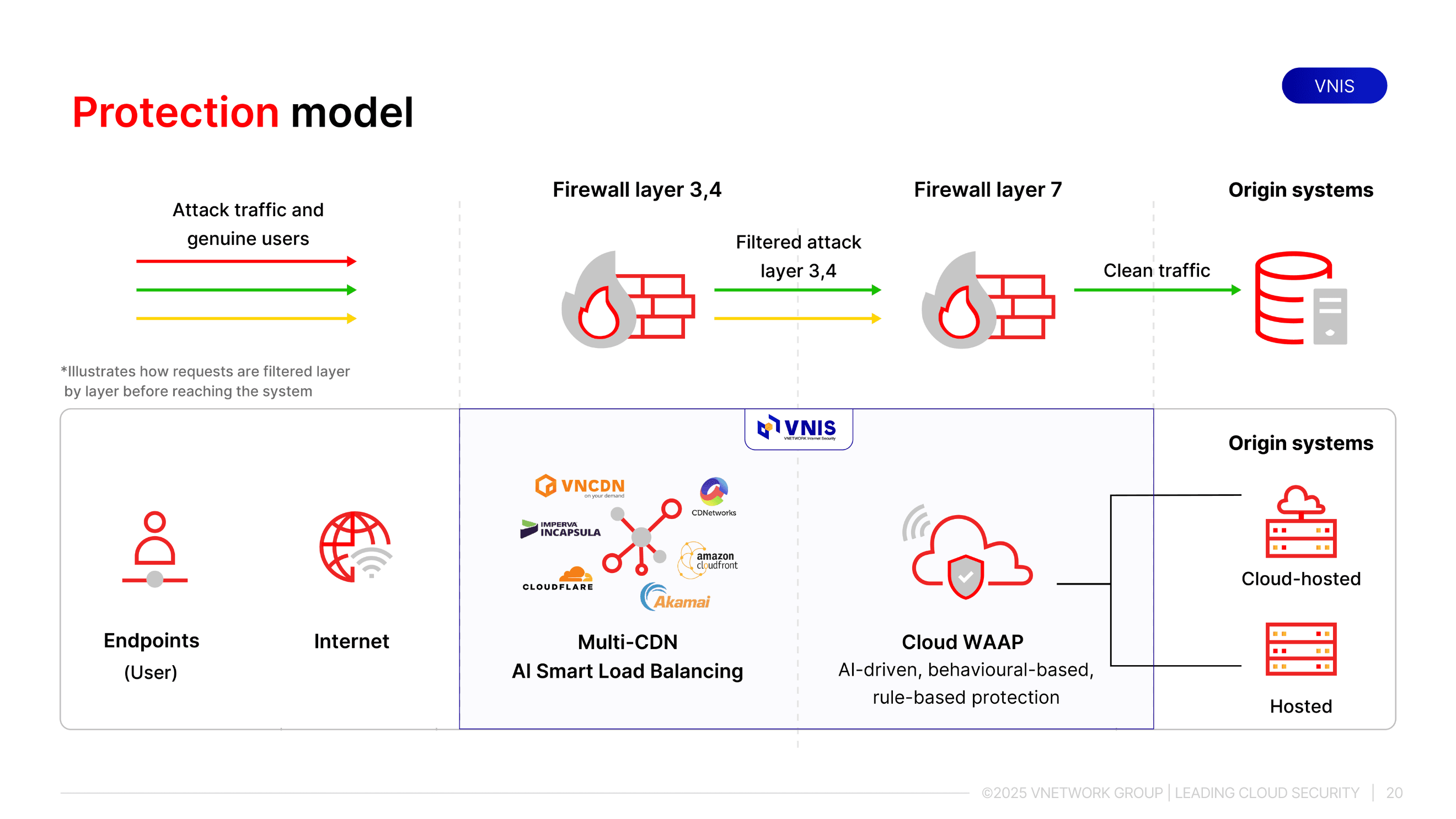
Two-layer protection architecture: CDN + WAAP
VNIS operates on a two-layer protection model:
- Multi-CDN layer: Multi-CDN network of 2,300+ PoPs across 146+ countries, including all major Vietnamese ISPs (FPT, VNPT, Viettel, MobiFone). The CDN layer absorbs and disperses attack traffic at the source via local scrubbing, eliminating the need to route traffic to a centralized scrubbing center.
- WAAP layer: WAAP (Web Application and API Protection) delivers comprehensive application-layer defense, combining WAF, bot management, API protection, and Layer 7 DDoS mitigation in a single platform.
Three core technologies powering VNIS
| Technology | How it works | Real-world application |
| AI-Driven Awareness | Applies AI to analyze context and behavior, detecting complex logic-based attacks with no prior signature | Identifies compromised accounts even without known bad IPs; detects zero-day attacks |
| Rule-Based | Applies 2,400+ rules based on OWASP to block known and common attack patterns | Blocks SQL injection, XSS, brute force, and OWASP Top 10 vulnerabilities |
| Behaviour-Based | Monitors user behavior to distinguish real humans from bots and automated attacks | Stops fake account registration bots, form spam, click farms, and credential stuffing |
Case study: FireAnt — system restored in the same night as the attack
FireAnt is a platform providing investment tools and financial data for the Vietnamese stock market, serving tens of thousands of individual and institutional investors. System availability is critical, particularly during peak trading hours.
Before partnering with VNETWORK, FireAnt faced two serious challenges: prolonged DDoS-induced outages and poor data delivery performance that directly impacted customer experience during trading sessions. When an urgent alert came in the middle of the night, VNETWORK rapidly isolated the attack using VNIS's Multi-CDN infrastructure, activating global CDN nodes for immediate response while simultaneously optimizing content delivery to restore trading performance for users.
Results achieved:
- FireAnt's system was protected and fully stabilized on the same night the attack occurred, with no service disruption reaching end investors.
- Successfully withstood sustained attacks exceeding 150 Gbps of attack traffic per day for several months, with no infrastructure upgrades required.
- Data delivery performance improved noticeably, especially during peak trading windows where every second of latency can affect investment decisions.
- FireAnt's engineering team no longer needs to respond manually to every attack. All mitigation is handled automatically by VNIS and monitored 24/7 by VNETWORK's SOC.
2. Cloudflare's Anti-DDoS service
Cloudflare is a globally recognized name in the cybersecurity field. The company offers a cloud-based DDoS protection service that defends against Layer 3, 4, and 7 attacks. Cloudflare leverages its vast global network to mitigate the impact of DDoS attacks. Users can choose between a free plan and an enterprise plan. The free plan provides basic DDoS protection suitable for small, simple attacks; for larger attacks, the website may be blocked. The enterprise plan offers advanced security features, with additional costs for each integrated feature.
Key features:
- Mitigation capacity of up to 100 Tbps.
- Extensive global CDN network.
- Integrated WAF (Web Application Firewall).
- Rate limiting to control traffic from access points.

3. Imperva's DDoS protection service
Imperva is a multi-cloud security platform designed to protect applications and databases. Imperva provides DDoS protection with over 44 DDoS Scrubbing Centers, stopping attacks on Layers 3, 4, and 7. The company currently offers solutions for various sectors, including e-commerce, finance, gaming, manufacturing, and technology.

Key features:
- Protects websites, networks, DNS, and individual IPs.
- Mitigation capacity of 9 Tbps and 65 Gpps.
- Imperva offers a 3-second mitigation SLA for any DDoS attack, regardless of type, size, or duration, without disrupting legitimate traffic.
- Provides real-time visibility into DDoS threats with correlated reporting and attack analysis.
4. Radware's DDoS protection service
Radware delivers a cloud-based anti-DDoS service for enterprises and service providers. The Radware system is capable of securing private clouds, public clouds, and 5G infrastructure for large-scale networks.
Key features:
- Flexible and scalable attack mitigation configurations.
- Can be tailored to the requirements of different clients, such as telecom operators and cloud providers.
- Protects against zero-day vulnerability exploits.

5. Akamai's Anti-DDoS service
Akamai offers the Kona DDoS Defender, a cloud-based security solution capable of stopping various types of DDoS attacks, including UDP, SYN, HTTP GET, and POST floods. The Kona DDoS Defender combines a Security Operations Center (SOC) with Akamai's intelligent security platform to keep business websites operational even when under attack.
Key features:
- Akamai's SOC operates 24/7.
- A management dashboard displays real-time traffic information for easy monitoring.

6. AWS shield's anti-ddos service
AWS Shield is a DDoS protection service developed by Amazon Web Services for applications running on AWS. AWS Shield provides protection against Layer 3, 4, and 7 attacks. There are two tiers: AWS Shield Standard and AWS Shield Advanced. AWS Shield Standard is a free version that offers protection against common DDoS and transport layer attacks. For enhanced protection, AWS Shield Advanced provides greater mitigation capacity for larger DDoS attacks and includes support from a dedicated team of engineers who can manually intervene to mitigate severe attacks.

Key features:
- Blocks Layer 3, 4, and 7 DDoS attacks.
- Load-balancing CDN.
7. Sucuri's DDoS protection service
The Sucuri Website Firewall is a security solution designed to prevent DDoS attacks on websites, developed by the security company Sucuri. Sucuri's DDoS protection service is cloud-based and protects websites from various hacker attacks, including DDoS and malware. The security system combines a WAF (Web Application Firewall), IDS (Intrusion Detection System), and CDN (Content Delivery Network).
Key features:
- DDoS prevention and mitigation.
- Vulnerability patching and system hardening.
- Blocks zero-day vulnerability exploits.
- CDN with routing capabilities to reduce network load and improve performance.
8. Netscout's DDoS protection service
Netscout offers a range of products and services to defend against sophisticated application-layer DDoS attacks. This DDoS protection service helps block attacks on mobile applications, ensuring performance and accessibility on mobile networks. Netscout provides various deployment models, including on-premise software and virtualized solutions.
Key features:
- Blocks DDoS attacks on customer networks with attack traffic up to 140 Tbps.
- Operates on either IPv4 or IPv6 protocols.

9. Link11's DDoS protection service
Link11 develops cloud-based security solutions to protect websites and IT infrastructure from DDoS attacks. Link11 uses AI to automatically filter malicious traffic to servers, provides 24/7 support based in Europe, and can quickly set up security systems for new clients to ensure a timely response during an attack.
Key features:
- Website DDoS protection.
- CDN load balancing.
- Provides cybersecurity threat intelligence.
- Bot management.
- WAF to block zero-day vulnerability exploits.
A comprehensively secured network not only prevents hacker intrusions but also improves service delivery and encourages online customer engagement. Therefore, investing in DDoS protection is essential if you want your online business to survive and thrive sustainably.
FAQs – Answering your DDoS questions
1. What is DDoS and how dangerous is it?
DDoS stands for Distributed Denial of Service. It's an attack that overloads a website with traffic, causing it to crash and become unavailable. It is very dangerous as it can disrupt business operations and damage your reputation.
2. How is a DDoS attack different from website hacking?
A DDoS attack aims to overwhelm a system with junk traffic to make it unavailable. Hacking, on the other hand, aims to infiltrate a system to steal or control data. One causes a disruption, while the other involves unauthorized access.
3. Do small businesses need DDoS protection?
Yes. Small businesses often have weaker security, making them easy targets. A DDoS protection service ensures business continuity and saves on potential recovery costs.
4. How long does it take to deploy a DDOS protection solution?
It can take from a few hours to a few days, depending on the system's scale and the provider. Cloud-based services offer the fastest and most effective deployment.
5. Will DDoS protection slow down my website?
No. On the contrary, if you use a service that includes an integrated CDN, your website's performance will likely improve.
6. Should I choose a local or an international provider?
A local provider is often suitable for businesses operating domestically, offering faster support and optimized costs. An international provider is better for global businesses that require a large, distributed infrastructure.