1. What is a botnet?
A botnet is a network of internet-connected devices that have been infected with malware and are remotely controlled by hackers, typically without the knowledge of the device owners. Each device in the network is referred to as a "bot" or "zombie," and the entire system can consist of tens of thousands to millions of devices spread across the globe.
To better understand botnet networks, it is important to distinguish between a few core concepts:
- Bot (zombie computer): A device infected with malware and controlled by a hacker without the owner's consent.
- Botnet (Bot Network): A collection of bots that are coordinated to act simultaneously based on commands from a central source.
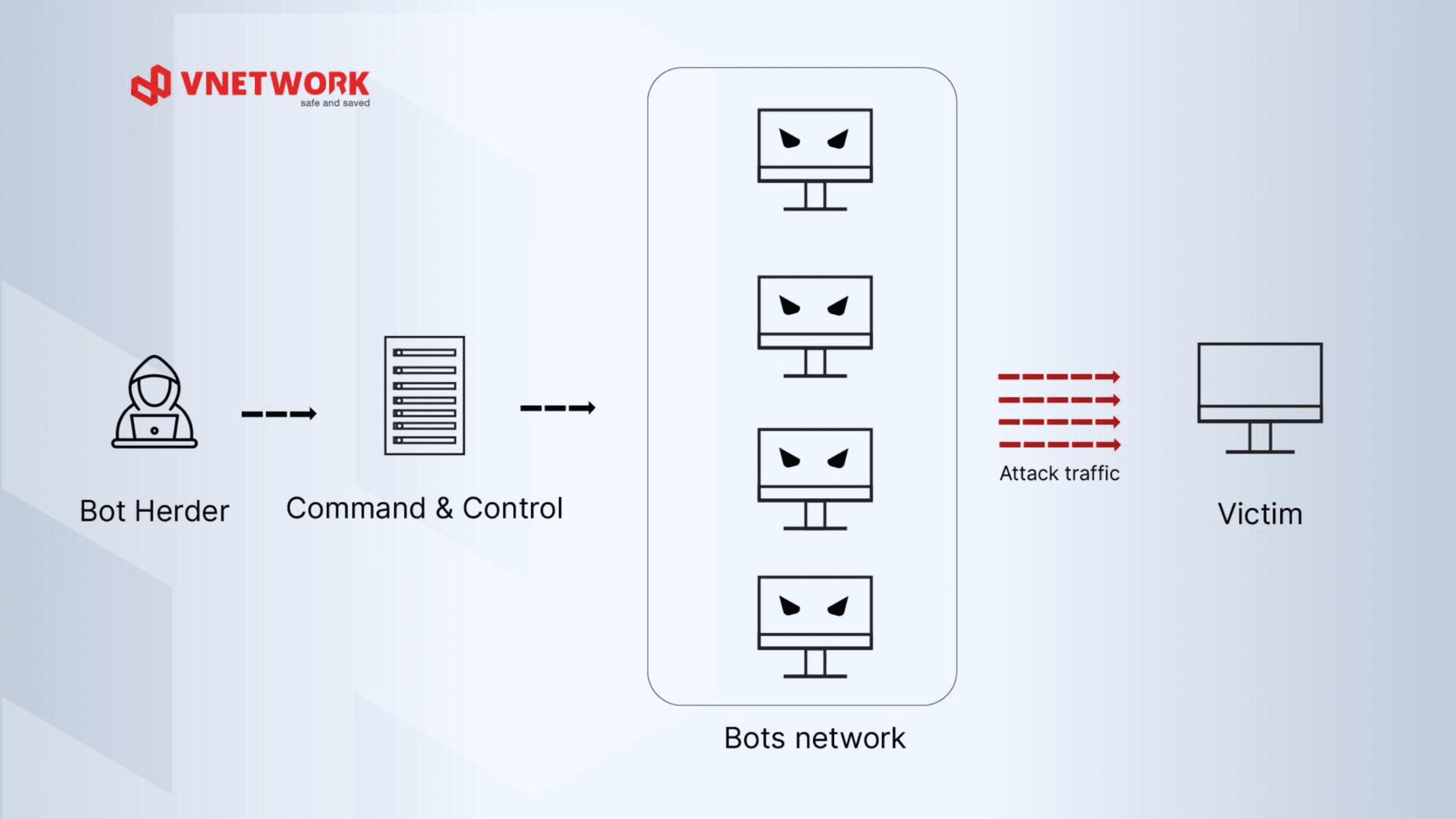
- Bot Herder: The hacker or cybercriminal group behind the operation of the entire botnet, issuing commands and exercising remote control.
- C&C Server (Command & Control): The central server that the Bot Herder uses to send commands to the entire botnet. It is the "brain" of the entire attack network.
Unlike conventional malware that only targets a single device, botnets are distributed and synergistic in nature, meaning attack capability grows exponentially as more bots are added to the network.
2. How does a botnet network operate?
The process of building and operating a botnet unfolds across three consecutive stages, from infecting devices to executing attacks.
Stage 1: Device infection
The first stage is when hackers implant malicious code onto victims' devices. Common infection vectors include:
- Phishing email: Users are tricked into opening attachments or clicking malicious links in phishing emails disguised as legitimate communications, after which bot malware is automatically downloaded and installed.
- Exploiting software vulnerabilities: Attackers target unpatched vulnerabilities in operating systems, browsers, or applications to inject malware without any user interaction.
- Malware spreading through internal networks: An infected device can automatically search for and propagate to other devices on the same network. Malware such as trojans and worms are the most common infection methods.
- Unsecured IoT devices: IP cameras, routers, and smart devices with default passwords or outdated firmware are preferred targets because they typically lack antivirus software.
Stage 2: Connecting to the C&C server
Once infected, each bot automatically connects to the C&C Server to "register" in the botnet and await commands. This connection is typically concealed within normal network traffic, making detection difficult.
Attackers are increasingly using more sophisticated C&C mechanisms, most notably the peer-to-peer botnet model, where bots communicate with each other rather than relying on a single central server, making it far more difficult to neutralize the botnet.
Stage 3: Executing attack commands
Once the Bot Herder issues commands, the entire botnet acts in unison. Common behaviors include:
- Launching large-scale DDoS attacks to take down target systems
- Sending mass spam email or phishing campaigns
- Stealing login credentials and financial data from infected devices
- Cryptomining using the victim device's resources
- Installing additional malware such as ransomware or spyware onto controlled devices
3. Common DDoS botnet attack methods
DDoS botnet attacks occur with high frequency and at massive scale. Attackers use a large number of bots to send floods of access requests to a target, pushing the system into an overloaded state, consuming all available bandwidth, and rendering network services inoperable.
DDoS botnets also disrupt enterprise online services, including e-commerce stores, online banking, and mobile applications, degrading the user experience and significantly impacting brand reputation and revenue.
DDoS botnets come in many variants targeting different layers of the OSI model. Understanding each attack type helps organizations select the right defensive solution.
TCP SYN Flood
This attack exploits the three-way handshake mechanism of the TCP protocol. Bots continuously send SYN packets to the server but never complete the final acknowledgment step, forcing the server to keep thousands of half-open connections in memory until resources are completely exhausted.
UDP Flood
Bots send a large volume of UDP packets to random ports on the target server. The server must constantly check whether any application is listening on each port, consuming all bandwidth and processing capacity until the system can no longer respond.
HTTP Flood and Spidering
This is the most complex attack method because bots simulate real user behavior, sending valid HTTP Flood GET or POST requests to the web application. The spidering variant automatically crawls and follows internal links, generating an enormous load at Layer 7 that conventional firewalls struggle to filter.
4. Impact of DDoS botnets on businesses
When attacked by a botnet network, businesses face serious consequences across multiple dimensions.
- Service disruption and downtime: The flood of requests from a botnet pushes systems into an overloaded state, preventing legitimate users from accessing services. Downtime can last from a few minutes to several days depending on the scale of the attack and the responsiveness of existing security systems.
- Loss of system control: When a botnet penetrates deep into the infrastructure, internal devices become "zombies" operating under hacker control. These devices can be used to distribute malware, send spam, attack other targets, or steal internal data without any warning.
- Financial losses: The costs incurred during a botnet attack include incident remediation, emergency security system upgrades, compensation for affected partners and customers, as well as actual revenue lost during the entire period of downtime.
- Data security vulnerabilities and legal exposure: Botnets not only cause congestion but also open the door to sensitive data theft. When customer data is leaked, businesses risk facing penalties under the Personal Data Protection Law and applicable cybersecurity regulations.
5. How to check whether a device is infected with a botnet
Early botnet detection is a critical factor in minimizing damage. Initial signs are often subtle and easy to overlook without a systematic monitoring process.
Signs that a device may be infected with a bot
Common warning signs to watch for:
- Abnormally high CPU or RAM usage with no active tasks running
- Sudden spike in outbound network traffic, particularly at night or outside business hours
- Slow device performance or unexplained application latency
- Unknown processes appearing in Task Manager or the process list
- Connections to unidentified IP addresses or suspicious domains
- Security software being automatically disabled or unable to update
Checking with tools and techniques
The following are technical checks that can be performed directly within an enterprise environment:
- Outbound traffic analysis: Use network monitoring tools to track external connections. A continuous connection to a fixed IP address on an unusual port is a classic sign of communication with a C&C Server.
- System process inspection: Review the running process list to identify unknown processes. On Linux, the command "netstat -antp" allows you to instantly view active network connections along with their corresponding processes.
- System log review: Analyze system logs and firewall logs to look for unusual connections, especially failed connection attempts or connections to IP ranges on blocklists.
- Scanning with dedicated security tools: Run a comprehensive scan using up-to-date anti-malware software to detect bot files or rootkits that may have concealed themselves in the system.
Response when an infected device is detected
- Immediately isolate the device from the internal network to prevent the botnet from spreading to other devices
- Capture the system state (memory dump, logs) to support root cause investigation
- Scan and remove malware; in cases of severe infection, restoring from a clean backup is the safest approach
- Change all related credentials: account passwords, API keys, and SSL certificates
- Patch the exploited software vulnerabilities to prevent reinfection
6. Effective strategies for defending against DDoS botnets
Defending against botnets requires a multi-layered strategy that combines technology with rigorous operational processes. Below are four core solution categories.
Firewalls and intrusion detection/prevention systems (IDS/IPS)
Firewalls serve as the first filtering layer, controlling all incoming and outgoing network traffic based on predefined rules. When integrated with a next-generation WAF, the system can identify and block abnormal traffic patterns characteristic of botnets.
IDS monitors and alerts when intrusion signs are detected, while IPS goes one step further by automatically intervening and blocking attacks immediately without waiting for a manual response from the technical team.
Web application and API protection (WAAP)
For application-layer botnet attacks such as HTTP Flood, WAAP combines WAF, API protection, bot mitigation, and DDoS defense into a unified platform, enabling precise differentiation between real users and automated bots.
In addition to blocking SQL injection and XSS attacks, WAAP continuously updates its detection of new botnet attack vectors, including variants that use artificial intelligence to evade detection.
Distributed CDN infrastructure
Deploying a CDN distributes attack traffic across multiple Points of Presence (PoPs) worldwide instead of concentrating it all on the origin server. When a botnet strikes, the CDN absorbs and handles the bulk of traffic at the PoPs closest to the attack source, protecting the origin server from overload.
Real-time network traffic monitoring
Establishing a continuous monitoring system allows the technical team to detect anomalies early before they escalate into serious incidents. Key indicators to monitor include sudden traffic spikes from a specific IP range, abnormal request rates to a particular endpoint, and outbound connections to unidentified addresses.
7. VNIS - A comprehensive DDoS botnet defense solution for businesses
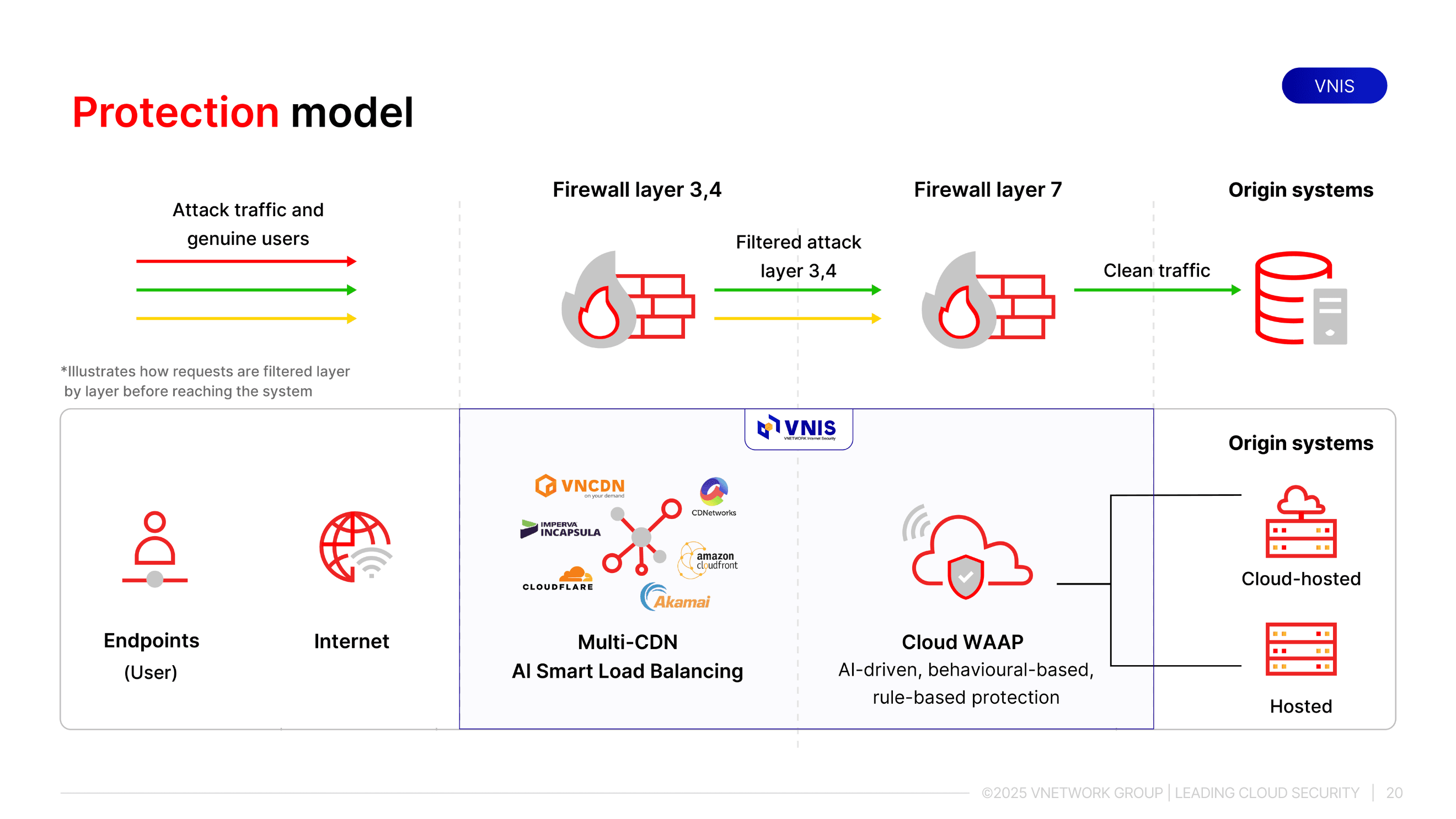
VNIS (VNETWORK Internet Security) is VNETWORK's website security platform, built to help businesses proactively defend against cybersecurity threats, including multi-layer DDoS botnet attacks from Layer 3/4 to Layer 7.
Beyond its security capabilities, VNIS also maintains website and application speed and stability even under high-traffic conditions. The solution operates on a global infrastructure with 2,300+ PoPs across 146+ countries, capable of handling traffic up to 2,600 Tbps and more than 10 billion requests per day. With 2,400+ active security rule sets, VNIS currently protects 400,000+ websites, applications, and APIs, keeping systems ready to withstand large-scale DDoS attacks.
Two-layer protection model
- Layer 1 - Infrastructure protection: VNIS combines AI Smart Load Balancing and Multi-CDN to handle DDoS attacks at the network layer. When a botnet strikes, AI automatically analyzes access behavior, distributes traffic intelligently, and eliminates anomalous traffic sources before they overload the system, without disrupting legitimate users.
- Layer 2 - Application layer protection: VNIS deploys an AI-powered WAAP to block Layer 7 DDoS attacks, malicious bots, and common security vulnerabilities listed in OWASP Top 10. This layer protects the processing logic of web, app, and API systems directly, where botnets typically probe deepest and are hardest to detect.
8. Conclusion
Botnets are a sophisticated and dangerous threat due to their distributed nature, difficulty of detection, and capacity to cause harm across multiple dimensions simultaneously. Understanding what a botnet is, mastering how to identify signs of infection, and deploying appropriate layers of defense are the foundations for businesses to protect their systems sustainably.
For organizations with critical web infrastructure or online services that require high uptime, an integrated solution like VNIS simplifies the entire defense process and proactively blocks botnets before damage occurs. Contact VNETWORK via Hotline (028) 7306 8789 or email contact@vnetwork.vn for tailored advice based on your organization's scale and infrastructure.
FAQ: Frequently asked questions about botnets
1. How is a botnet different from a regular virus?
A regular virus typically operates independently on the infected device, while a bot is malware specifically designed to connect to a central server and operate under the coordination of a hacker. This allows bots to receive commands and execute different behaviors over time, without being limited to a single fixed objective like a conventional virus.
2. Can IoT devices be infected with a botnet?
Yes. IoT devices such as IP cameras, routers, and smart TVs are common botnet targets because they often run outdated firmware, use default passwords, and receive infrequent security updates. Businesses should change default passwords and regularly update firmware for all IoT devices on their networks.
3. Are small businesses targets of botnets?
Yes. Small and medium-sized businesses are often easier targets because their security infrastructure is more limited, while customer data and financial assets remain valuable resources for attackers. Additionally, devices on small business networks can be conscripted as bots to attack larger targets.
4. Can a botnet be completely dismantled?
Completely dismantling a large botnet network is extremely difficult because bots are distributed across multiple countries and C&C Servers change frequently. For businesses, the more practical goal is building sufficiently strong defenses to avoid becoming a victim or becoming part of a botnet.
5. How does VNIS protect businesses from botnets?
VNIS combines Cloud WAF, AI Load Balancing, and a global multi-CDN network to detect and block DDoS botnet attacks in real time. When anomalous botnet traffic is detected, the system automatically distributes traffic across CDNs in the alliance, absorbing the entire attack volume before it reaches the business's origin server.