1. What is man in the middle?
Man in the middle (MITM) is a type of attack in which the attacker secretly inserts themselves between two communicating parties, typically a user and a server, to eavesdrop, steal, or tamper with data without either party being aware.
The name "man in the middle" accurately reflects the nature of this attack: the adversary stands in the middle of a legitimate communication channel and gains full control over the data flowing through it. From the victim's perspective, everything appears normal since the connection is still active and responses are still received, yet in reality all content has been read or altered by a third party.
A MITM attack typically unfolds in two successive phases. During the interception phase, the attacker positions themselves within the communication stream using techniques such as IP spoofing, DNS spoofing, or setting up a rogue Wi-Fi hotspot. During the decryption phase, the attacker processes the intercepted data by downgrading encrypted connections, stealing SSL certificates, or hijacking active sessions. This combination of two phases makes MITM a comprehensive threat that is harder to detect than many conventional forms of cyberattack.
2. Objectives of MITM attacks and their impact on business operations
Man-in-the-middle attacks do not only target personal data; they also trigger a chain of serious consequences for an organization's operations. Understanding both dimensions - what the attacker is after and the actual damage the organization sustains - is the first step toward building an effective defense strategy.
2.1. What does the attacker seek?
Actors carrying out man-in-the-middle attacks typically pursue one or more of the following objectives:
- Stealing authentication credentials: Usernames, passwords, OTP codes, session tokens, and API keys. These are often a stepping stone for deeper access into internal infrastructure.
- Harvesting sensitive data: Credit card information, business contracts, internal documents, and customer data. Attackers may sell these datasets on darknet markets or use them for extortion.
- Forging and manipulating content: Modifying packets in transit to alter transaction details, bank account numbers, or inject malware into web page content.
- Long-term espionage: Monitoring an organization's communication flows for weeks or months to gather intelligence in preparation for larger-scale attacks such as ransomware or supply chain compromises.
2.2. What damage does the organization sustain?
Beyond stolen data, MITM attacks leave a compounding impact at both the operational and legal levels. When a data breach occurs through a MITM channel, investigation and remediation typically take longer because the attack leaves fewer clear traces than conventional intrusion methods. During that period, organizations face the following concrete losses:
- Service disruption and revenue loss: Transaction processing systems, payment gateways, or internal communication platforms may be taken down during incident detection and response, which is especially severe for financial services and e-commerce businesses.
- Direct financial loss: Attacks targeting transactional email can cause funds to be transferred to accounts controlled by the attacker, and are often difficult to recover due to the speed of international payment systems.
- Legal and compliance risk: Organizations that handle user data are obligated to protect it under cybersecurity laws and personal data protection regulations. Violations resulting from MITM attacks may lead to administrative penalties or civil liability.
- Loss of customer and partner trust: This is often the longest-lasting and hardest-to-quantify form of damage. Once a security incident becomes public, the organization must invest significantly in rebuilding its brand reputation.
3. Common man-in-the-middle attack techniques
MITM attacks do not come in a single form. Attackers choose the technique best suited to the target network environment and specific objective. The following are the six most common techniques, ordered from the network layer to the application layer.
3.1. IP spoofing
IP spoofing is the foundational technique behind many MITM attacks. The attacker modifies IP packet headers to forge the source address, tricking the target system into believing the data originates from a legitimate device. As a result, network traffic is redirected to the attacker's machine rather than its true destination. This technique is typically the first step in establishing a MITM position, laying the groundwork for more sophisticated follow-on techniques. A solid understanding of the OSI model helps technical teams recognize that IP spoofing operates at the network layer (Layer 3), where packet routing is controlled.
3.2. DNS spoofing
DNS spoofing, also known as DNS cache poisoning, occurs when an attacker injects fraudulent DNS records into the cache of a DNS server. When a user navigates to a legitimate domain name, they are redirected to an IP address controlled by the attacker without noticing any anomaly since the browser still displays the correct domain name. This technique underpins many large-scale phishing campaigns and is particularly dangerous when targeting online banking systems, payment gateways, and enterprise authentication services.
3.3. HTTPS spoofing
HTTPS spoofing exploits users' trust in the security lock icon displayed by their browser. The attacker sets up a fraudulent website using a domain name that closely resembles a legitimate one, combined with a valid SSL certificate issued for that fake domain. The user sees an apparently normal HTTPS connection but is actually interacting with the attacker's infrastructure. This technique frequently accompanies vulnerabilities listed in the OWASP Top 10 and is the mechanism behind many spear phishing campaigns targeting finance staff and senior executives.
3.4. SSL hijacking and SSL stripping
These two techniques both target the TLS/SSL security layer but operate through different mechanisms. In SSL stripping, the attacker downgrades an HTTPS connection to plain HTTP during transit, causing data to pass through in unencrypted plaintext. The user still sees the correct domain name but no longer has a genuinely secure connection. In SSL hijacking, the attacker relays forged authentication keys to both sides during the TCP handshake, establishing a session that appears secure but is fully controlled. Both techniques are especially dangerous on public Wi-Fi networks, where traffic has not been filtered through a corporate firewall.
3.5. Email hijacking and email spoofing
In a corporate environment, attackers can intercept and impersonate email flows between parties, which is particularly dangerous in financial transactions. Email spoofing combined with MITM allows adversaries to change bank account numbers in wire transfer emails without the recipient suspecting anything, resulting in direct financial losses that are difficult to recover. Email hijacking is more sophisticated: the attacker gains access to an actual mailbox, monitors the full exchange, then intervenes at precisely the moment a transaction takes place. The absence of authentication standards such as DKIM and DMARC leaves organizations vulnerable to this technique.
3.6. Wi-Fi eavesdropping
The attacker creates a rogue Wi-Fi hotspot with the same name as a legitimate network at public locations such as airports, coffee shops, or conference centers. Once a user connects, all network traffic passes through the attacker's device. This is one of the easiest MITM scenarios to execute and one of the hardest for end users to detect. Remote workers using public Wi-Fi without a VPN represent the highest-risk group. This technique is commonly combined with SSL stripping to neutralize the remaining encryption layer, creating a complete MITM attack using only consumer hardware and readily available software.
4. Signs of a man-in-the-middle attack
Most MITM attacks are designed to operate silently; however, there are four groups of technical indicators that IT teams should watch for, each typically pointing to a specific attack technique:
- Unusual SSL certificate warnings: Mismatched SSL certificates, unexpectedly expired certificates, or "untrusted" warnings when accessing familiar sites are signals of ongoing HTTPS spoofing or SSL hijacking. Users should never dismiss these warnings, especially on sites handling financial transactions or login credentials.
- Abnormally slow connections or unexpected redirects: Significantly increased response times with no clear technical cause, or a browser repeatedly redirecting to unfamiliar URLs when accessing known sites, is typically a sign that DNS spoofing or IP spoofing is routing traffic through an intermediate point.
- Unknown MAC addresses in the ARP table and abnormal network traffic: When auditing the ARP tables of devices on the internal network and encountering an unfamiliar MAC address mapped to the IP of the gateway or a critical server, this is a classic indicator of ARP spoofing, often deployed alongside Wi-Fi eavesdropping in open-office environments.
- Sessions dropping unexpectedly and repeated authentication failures: Users being logged out for no apparent reason, sessions expiring abnormally, or system logs recording many failed authentication attempts from the same IP within a short window are often signs of session hijacking or brute force attacks being used in conjunction with MITM to exploit stolen credentials.
5. Effective countermeasures against MITM attacks
No single measure is sufficient to fully prevent man-in-the-middle attacks, since each MITM technique exploits a different layer of the network infrastructure. An effective defense strategy requires a combination of multiple protection layers applied simultaneously at both the technical and human levels.
5.1. Deploy end-to-end encryption and SSL certificate protection
This is the direct countermeasure against SSL stripping, SSL hijacking, and HTTPS spoofing. All web applications and APIs must use HTTPS with valid certificates, combined with HSTS to prevent browsers from accepting unencrypted HTTP connections. Implementing Certificate Pinning for critical mobile applications adds protection against HTTPS spoofing. This is also a baseline requirement for meeting the ISO 27001 standard.
5.2. Secure email against hijacking and spoofing
To defend against email hijacking and email spoofing, organizations must deploy three authentication standards simultaneously: SPF to verify the sending mail server, DKIM to digitally sign each email and detect forgeries, and DMARC to define the handling policy for emails that fail authentication. For financial transactions conducted over email, out-of-band verification such as a phone call should be required before any wire transfer is executed.
5.3. Network segmentation and continuous monitoring
Network segmentation directly limits the scope of damage that IP spoofing and DNS spoofing can cause. Combined with a Defense in Depth strategy, each network segment has its own access controls, forcing an attacker to bypass multiple layers of enforcement rather than moving freely after breaching a single entry point. Integrating firewall controls at each segment boundary alongside anomaly detection for the ARP table enables early identification of IP spoofing and ARP-based MITM activity.
5.4. Adopt a Zero Trust model
The Zero Trust principle is particularly effective at neutralizing the consequences of Wi-Fi eavesdropping and session hijacking. When every access request must be continuously authenticated regardless of network location, gaining a MITM position no longer automatically grants the attacker access to internal resources.
5.5. Protect the application layer with WAF and WAAP
Deploying a WAF helps detect and block abnormal requests, including indicators of session hijacking and vulnerability exploitation accompanying MITM. A WAAP solution with integrated AI enables real-time behavioral analysis, identifying anomalous traffic patterns and responding immediately when attack indicators are detected, including MITM variants targeting APIs.
5.6. Build security awareness through staff training
Wi-Fi eavesdropping and HTTPS spoofing are most effective when employees lack security awareness. Social engineering campaigns often lure employees into connecting to unsafe networks or dismissing SSL certificate warnings. Regular training, combined with strict verification procedures for financial transactions conducted via email and a mandatory VPN policy for working outside the office, forms an indispensable layer of defense.
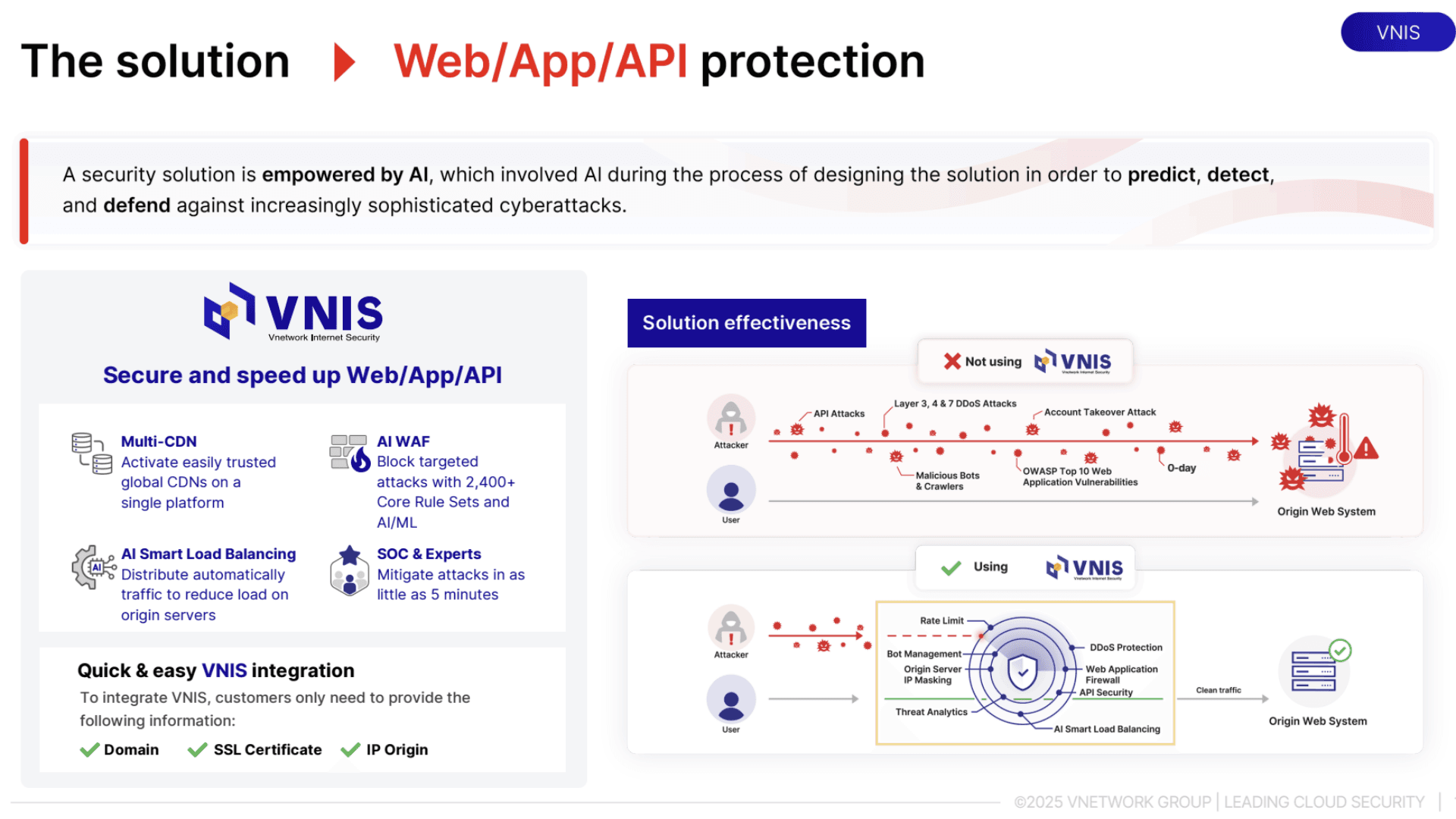
6. VNIS: Security solution for Web, App, and API systems
VNIS (VNETWORK Internet Security) is a security platform that protects Web, App, and API assets against Internet-borne threats. The system provides multi-layer DDoS mitigation (Layer 3/4/7) in real time while also addressing common threats such as malicious bots and application vulnerability exploitation. In addition, VNIS helps reduce the risk of man-in-the-middle attacks by enforcing HTTPS and other transport-layer security mechanisms.
The system applies a two-layer parallel protection model:
- Layer 1: AI Smart Load Balancing combined with Multi-CDN analyzes traffic and optimizes access distribution in real time. When traffic anomalies are detected, the system automatically reroutes traffic and isolates suspected sources to protect the infrastructure.
- Layer 2: An AI-integrated WAAP monitors the activity of web applications and APIs. The system detects abnormal behaviors such as bot traffic, vulnerability exploitation, and unauthorized access. The security rule set provides full coverage of the OWASP Top 10 and is continuously updated to address the latest attack variants.
7. Conclusion
Man-in-the-middle (MITM) attacks are not a theoretical threat but a real risk for every organization that transmits data over the Internet. Attack techniques are growing increasingly sophisticated and can emerge across multiple layers, including exploitation of network misconfiguration, attacks on the transport channel such as SSL stripping, and deception of users through rogue Wi-Fi hotspots and email phishing. To defend effectively, organizations must implement a multi-layered security strategy encompassing TLS/HTTPS encryption, network segmentation, Zero Trust architecture, continuous security monitoring, and user awareness training, all aimed at minimizing risk and improving early detection of threats.
FAQ - Frequently asked questions about man in the middle
1. What is man in the middle and why is it hard to detect?
Man in the middle (MITM) is an attack in which a malicious actor secretly inserts themselves between two communicating parties to eavesdrop on or forge data without either side being aware. It is difficult to detect because the connection continues to operate normally and victims still receive legitimate-looking responses, even though all content has already been read or altered by a third party.
2. What damage can a MITM attack cause to an organization?
A MITM attack can cause direct financial losses through manipulation of transactional emails, service disruption during incident response, legal exposure from data protection regulation violations, and long-term brand reputation damage. For financial services and e-commerce organizations in particular, the impact is often amplified by the real-time nature of transactions.
3. How do IP spoofing and DNS spoofing differ?
IP spoofing forges the source address in packet headers to redirect traffic at the network layer (Layer 3). DNS spoofing injects fraudulent DNS records into a DNS server's cache to misdirect users to an incorrect IP address at the domain resolution layer. IP spoofing is typically the first step in establishing a MITM position, while DNS spoofing directly deceives users into accessing fraudulent infrastructure.
4. How can I tell if I am under a man-in-the-middle attack?
Four groups of indicators to watch for: unusual SSL certificate warnings when visiting familiar sites; abnormally slow connections or unexpected redirects to unfamiliar URLs; unrecognized MAC addresses in the ARP table mapped to gateway IPs; and sessions dropping unexpectedly combined with a high volume of authentication failures in system logs.
5. How does VNIS protect organizations against MITM attacks?
VNIS applies a multi-layer security model to mitigate the risk of MITM attacks. At the infrastructure layer, the system combines Smart Load Balancing and Multi-CDN to analyze traffic in real time, detect anomalies, and filter suspected access before it affects the system. At the application layer, the WAAP platform monitors web, app, and API activity to detect behaviors such as session hijacking and malicious bots. VNIS also operates a 24/7 SOC team for timely detection and response to emerging threats.
