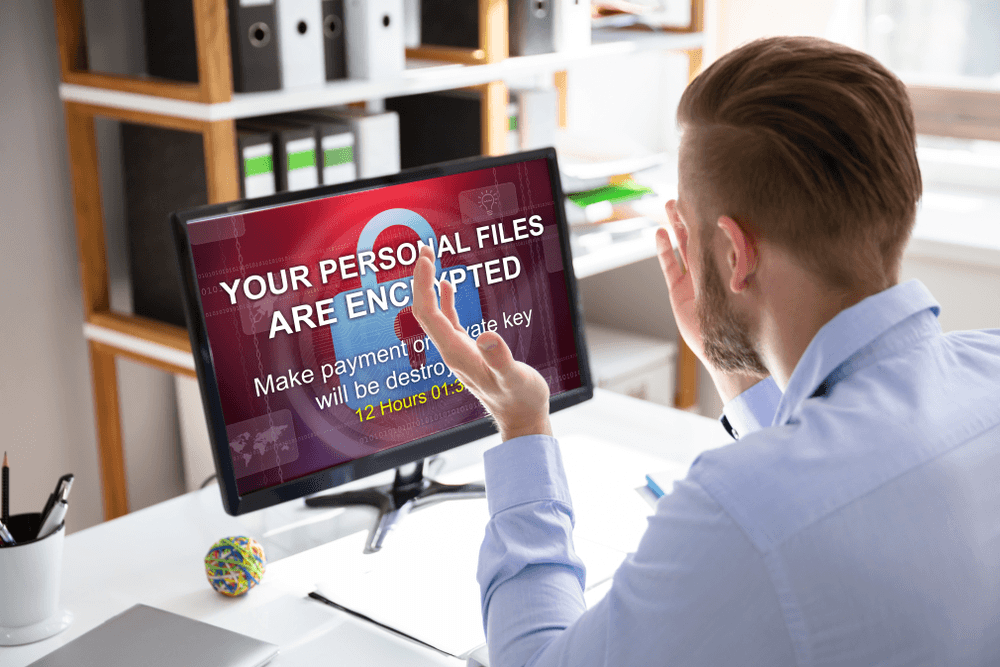
Ransomware is an extremely dangerous type of malware and is not easily detected. That is also why ransomware has become such a hot topic and always a threat to many Vietnamese businesses as well as the world.
Ransomware is considered one of the biggest malware threats in 2018 and it continues to disrupt the activities of businesses and the lives of users around the world in 2019. Security researchers has been tracking more than 1,100 different ransomware variants and this number has been increasing recently. Enough to show that ransomware is getting more sophisticated and cybercriminals have been actively creating a lot more ransomware. Below is a list of some of the most notorious ransomware in recent years that you should know about taking timely precautions.
1. Bad Rabbit
The Ransomware Bad Rabbit comes after WannaCry and NotPetya malicious codes on a larger scale and has infected major organizations in Russia and Eastern Europe. ESET and Proofpoint security experts said that Bad Rabbit was originally distributed via a fake Adobe Flash update package, but ransomware also has its own tool to move inside the network. This also explains why Bad Rabbit spread so quickly in such a short time.
If the user clicks on the malicious installer, their computer will be locked and the victim will have to pay a ransom of approximately $ 280 Bitcoin for a period of 40 hours to make a payment.

Ransomware Bad Rabbit spread quickly in a short time
2. Cerber
Cerber is one of the worst types of ransomware that has become worse. In addition to encrypting files and ransom, it now has the ability to steal Bitcoin wallets and user password information.
Targeting Office 365 users and using elaborate phishing campaigns, Cerber has affected millions of users worldwide, except for post-Soviet countries. Victims will receive an email with the address of Microsoft Office containing malicious code. After opening the email, ransomware will quietly distribute and encrypt data on the user’s computer. When the encryption is complete, Cerber will leave ransom notices in .TXT, .HTML and .VBS formats in each folder containing encrypted data. The malware requires a ransom of 1.24 bitcoins (about $ 520) and the amount doubles if a week fails to pay the ransom.
3. Gandcrab

Hackers use spam emails to spread GandCrab malware
Gandcrab is a handful of ransomware that requires payment with cryptocurrencies and using top-level domain names (TLDs). Surprisingly, this TLD domain was not sanctioned by ICANN, so it provided an additional level of “security” for criminals.
Moreover, Gandcrab relies heavily on Microsoft Office Macros, VBScript and PowerShell Macros to avoid detection and use the ransomware-as-a-service (RaaS) model to optimize distribution while hackers just need to focus. into spam emails sent to users. The ransom amount to recover data can range from USD 400 - USD 1,000. After more than a year of dominating computer networks around the world, Gandcrab finally announced that it was shut down after collecting more than $ 2 billion from victims and security experts also launched a new decoder. best for GandCrab malware.
4. Katyusha
Katyusha is an encrypted ransomware trojan that was first discovered in October 2018. It encodes files with the .katyusha extension and requires a payout of 0.5 bitcoin ransom within 3 days. Katyusha threatens to reveal the victim’s data if the ransom is not paid and as well as previous backups will be “evaporated” by the ransomware. Hackers often use email attachments to spread Ransomware Katyusha. So far, no tool has been able to crack this malicious code.
5. LockerGoga
LockerGoga is a relatively new ransomware, but its damage is not small and it is predicted that the list of victims will continue to increase over time. The peculiarity of this malware differs from regular ransomware is that it will force the victim to exit the infected device, which often results in the victim being unable to see the ransom notice and instructions on how to recover the file.
In early 2019, LockerGoga ransomware attacked several businesses and manufacturers, causing significant damage. After its attack on French engineering consultancy Altran, it continued to infiltrate Norsk Hydro Group - one of the world’s largest aluminum and renewable energy groups in Norway and two companies. Large chemical company based in the United States.
6. Ryuk
Ryuk is also one of the malware on the list of new ransomware, first appeared in August 2018 and has since pocketed more than $ 3.7 million in Bitcoin as a result of the extortion of 52 victims. The channel doesn’t carefully protect its server or data. Just by looking at the proceeds and the number of victims is enough to show that the people behind this Ryuk malware are patient, ready to wait for the fat prey to act recklessly.
Ryuk’s way of attack is nothing new. Spam emails are sent to your business account. By accidental clicking on the email including the carefully created attachment, the hacker was able to gain control of the entire system.
More sophisticated, they also spent a year to choose their prey, eliminating businesses not big enough to blackmail. This leaves the companies in the spotlight and still not aware to enforce security policies promptly.
7. SamSam
SamSam is a ransomware category most commonly used in targeted ransomware attacks. SamSam has attacked a variety of American industries, primarily critical infrastructure such as hospitals and healthcare companies. Last year, the SamSam attack paralyzed the city of Atlanta for days and costed taxpayers nearly $ 17 million.
Unlike other ransomware campaigns that rely on phishing techniques to distribute, SamSam uses Remote Computer Protocol (RDP) to gain access to the victim’s network. So far, the largest ransom paid to decode a SamSam ransomware of a victim is worth $ 64,000 - a significant amount compared to most ransomware families.
Ransomware is preventable

Security solutions prevent ransomware attacks
As we have seen in recent years, threats from ransomware are growing in a scary way. Attacks occur with greater frequency, more sophisticated in attack methods, even backups cannot survive ransomware intrusion.
This is a fact that all businesses today need to take precautions. With email security system - Receive GUARD uses artificial intelligence technology and machine learning to analyze user behavior to help protect business data against any intending threats, including It’s new malware, not registered by any security agency in the world.
VNETWORK
Website: https://vnetwork.vn
Facebook: https://bit.ly/2Ee9HIK
Email: contact@vnetwork.vn
Hotline: (028) 7306 8789