1. What is a scam? Definition and related concepts
A scam refers to any deliberate act of deception in which an attacker uses fraudulent tactics to steal assets, data, or access credentials from a victim. In Vietnamese, "scam" translates to "lừa đảo" (fraud), and the term is now widely used in both personal and business contexts. Scams typically exploit psychological vulnerabilities rather than technical flaws, which means that even systems protected by a strong firewall can be compromised if employees lack awareness.
Scams are distinct from commonly confused terms: fraud (gian lận) is a broader legal concept; phishing is a specialized form of scam carried out via fake emails or websites to steal login credentials; and spam mail refers to unsolicited bulk messages that do not necessarily involve deceptive intent. The term "scam" is the broadest category, encompassing deception across any channel, including email, phone, social media, and in-person contact.

2. How does a scam work?
Unlike purely technical attacks, scams target people first and systems second. Scammers exploit social engineering to manipulate victims' emotions, inducing a psychological state that drives them to act without stopping to verify. Understanding this mechanism is the key to effective prevention.
2.1. The lifecycle of a scam attack
Regardless of format, most scam attacks follow five consistent stages:
- Stage 1 - Reconnaissance: The attacker gathers information about the target from social media, company websites, and business registration records to build a convincing scenario.
- Stage 2 - Initial contact: The attacker reaches out via email, phone, text, or social media with personalized content that references the target's name, job title, and company.
- Stage 3 - Building trust: The attacker maintains communication over days or weeks, sometimes completing small profitable transactions to establish credibility before making the main move.
- Stage 4 - Exploitation: The attacker requests sensitive information, a money transfer, a link click, or installation of a malicious application. Psychological pressure is maximized at this stage.
- Stage 5 - Disappearance: After achieving the objective, the attacker cuts off all contact. In BEC or financial scams, funds are typically routed through multiple intermediary accounts before the victim realizes what has happened.
2.2. Four psychological states scammers exploit
Each scam campaign is designed to push victims into one of four mental states that prevent them from verifying information before acting:
- Greed: Promises of prizes, attractive investment returns, or time-limited exclusive deals. Victims act out of fear of missing out on something valuable.
- Fear: Impersonation of government agencies, banks, or legal departments with warnings of fines, account freezes, or legal liability if the victim does not respond immediately.
- False trust: Impersonating a friend, a supervisor, a long-time partner, or a reputable brand so that the victim complies without question.
- Artificial urgency: Fabricated deadlines such as "within 2 hours," "today is the deadline," or "process before 5 PM" are designed to cut off the victim's ability to think, consult others, or verify information.
3. Why are scams increasingly difficult to detect?
Modern scams are no longer easily recognizable by typos or awkward grammar. Attackers now use AI to generate natural-sounding text, tailored in tone and style to specific audiences and professional contexts, and can even clone voices over phone calls using deepfake audio technology.

Combined with advanced email spoofing and domain-spoofing techniques, a professionally crafted scam email today looks completely indistinguishable from a legitimate message from a colleague or partner, even on visual inspection. Attackers also deliberately time their campaigns, such as sending them at month-end when workloads are high, or just before a holiday when employees process requests more quickly than usual.
Furthermore, modern scam campaigns may unfold over several weeks with multiple touchpoints before the decisive strike. By that point, the victim has accumulated enough trust to let their guard down. This is why technical verification through standards such as DKIM, SPF, and AI-based behavioral analysis has become an indispensable layer of defense, replacing subjective human judgment.
4. Common types of scams today
Understanding each type of scam helps individuals and businesses build appropriate defenses. The following are the most prevalent attack methods currently in use.
4.1. Email scam (scam mail)
Email scams are a form of phishing email sent in bulk to trick victims into providing information or taking harmful actions. Attackers typically use email spoofing to forge the sender's address. Common variants include: fake bank emails requesting account verification, prize notifications asking for an upfront fee, fraudulent invoices sent to accounting teams, and threatening messages impersonating legal authorities.
4.2. Social media and messaging scams
Attackers impersonate acquaintances, friends, or reputable brands to approach victims via messaging platforms. Common scenarios include impersonating someone the victim knows to request an urgent loan, organizing fraudulent mini-giveaways, or spreading malware through shortened links. Especially dangerous are campaigns that incorporate deepfake audio or images to increase credibility.
4.3. Financial and investment scams
Attackers construct fictitious investment schemes with attractive returns, then disappear with investor funds. Online job recruitment scams also fall into this category, where victims are required to pay a deposit before starting work. Personal information exposed through these incidents is frequently exploited in subsequent data breach campaigns.
4.4. Business Email Compromise (BEC)
BEC is a form of scam targeting businesses directly and typically causes the greatest financial damage. Attackers conduct spear phishing against personnel with financial authority, impersonating the CEO, CFO, or a partner to request urgent wire transfers or changes to beneficiary account details. Attackers tend to target domains with weak DMARC configurations to facilitate spoofing.
5. Five warning signs of a scam attack
Early identification is the most important line of defense. The following five signals should be checked immediately upon receiving any unusual request via email or message.
5.1. Urgent, pressure-driven language
Any message urging you to "act immediately," "within 24 hours," or "this is your last chance" should prompt verification before any action is taken. Artificial urgency is the primary tool scammers use to prevent victims from thinking critically. Apply a simple rule: the more urgent the request, the more carefully it must be verified before proceeding.
5.2. Unusual requests for sensitive information
No legitimate organization will ever request a password, OTP, bank card details, or national ID number via email or ordinary text message. If you receive such a request, even if the email appears to come from a bank or a colleague, treat it as a clear red flag. Refer to the 7 ways to identify a fraudulent email guide for a more comprehensive checklist.
5.3. Mismatched email address and domain
Always verify the sender's actual email address, not just the display name. Attackers use typosquatting to create look-alike domains such as "vnetw0rk.com" or "vnetwork-security.com." Additionally, a legitimate email must pass three layers of technical authentication: SPF, DKIM, and DMARC. Scam emails typically fail at least one of these checks upon technical inspection.
5.4. Suspicious attachments and links
Attachments with unusual extensions such as .exe, .zip, or .iso, or filenames mimicking legitimate documents, may contain trojans, spyware, or ransomware. For links, hover over them to preview the actual destination URL before clicking. Shortened links or URLs that do not match the brand name should be treated with caution, especially when they arrive via junk mail that has slipped into the main inbox.
5.5. Content inconsistent with the relationship context
An email appearing to come from a partner or colleague that makes an unusual request inconsistent with the history of your interactions, does not address you by name, or references incorrect details about your company is a sign that the account may be compromised. For financial requests, always verify by calling a phone number you have previously saved; do not call a number listed in the suspicious email itself.
6. Consequences of scams for individuals and businesses
The impact of a scam often spreads faster and lasts longer than victims initially anticipate. The following are the four most common categories of damage.
6.1. Direct financial loss
Financial losses from scams occur immediately and are usually unrecoverable, particularly once funds have been routed through multiple intermediary accounts before the victim detects the fraud. For businesses, losses extend beyond the stolen amount to include incident investigation costs, fees for engaging security firms to remediate the breach, and the cost of notifying affected parties.
6.2. Data leakage and risk of follow-on attacks
Information exposed through a single scam incident rarely results in just one loss. The stolen data may be sold on the dark web, used to install a rootkit for persistent access, or leveraged as the foundation for future data breach campaigns and targeted attacks against the organization. A leaked email address or phone number is the starting point for multiple subsequent attacks.
6.3. Brand reputation damage
A publicized scam incident, whether the organization was the victim or whether attackers misused its brand name to deceive others, causes serious erosion of trust among customers and partners. In sensitive industries such as finance, healthcare, or e-commerce, reputational damage can be more costly and longer-lasting than the direct financial loss itself.
6.4. Legal liability
Businesses may face compensation claims when customer data is exposed as a result of inadequate security measures. Regulations under the Personal Data Protection Law and the Cybersecurity Law are being progressively tightened, making proactive scam prevention a legal obligation rather than an optional precaution.
7. Effective scam prevention for individuals and organizations
7.1. Prevention measures for individual users
Individual users can reduce their risk by developing habits of verification before taking action:
- Verify the source by calling directly before fulfilling any financial request.
- Do not click links in emails or messages from unclear sources; instead, navigate directly to the official website.
- Never share OTPs, passwords, or bank card details through any channel other than the official application.
- Enable two-factor authentication (2FA) on all important accounts.
7.2. Protection measures for businesses and IT managers
At the organizational level, IT managers should apply a Defense in Depth strategy that combines technology, processes, and people:
- Conduct regular cybersecurity awareness training for all employees, with particular focus on finance and HR teams.
- Deploy intelligent email filtering systems; consult the ITU global email security standards to build an internationally compliant email policy.
- Establish financial transaction verification procedures with at least two levels of approval; never process wire transfers based solely on email instructions.
- Apply the Zero Trust principle to limit the blast radius when an account is compromised.
8. EG-Platform: A specialized email security solution to combat scams
8.1. Three-layer protection model
EG-Platform operates on a three-layer model, each layer independent yet sharing data with the others, forming a defense system with no blind spots:
- SpamGUARD: Uses machine learning and Bayesian filtering to score the risk level of each email. Simultaneously checks SPF, DKIM, and DMARC to detect domain spoofing. This layer filters and blocks scam emails, phishing mail, and malware-carrying messages at the outer perimeter.
- ReceiveGUARD: Sophisticated phishing emails that contain no malware are still detected through user behavior analysis and inspection of content, attachments, and URLs in a sandbox environment. When a risk is identified, suspicious links are neutralized before the user can access them. This layer detects 17 types of targeted attacks including BEC and APT, in compliance with ITU-T X.1236.
- SendGUARD: Controls outbound email to prevent compromised internal accounts from distributing spear phishing or leaking data. Filtering by IP, country, and sensitive content reduces the risk of incidents spreading outward from within the organization.
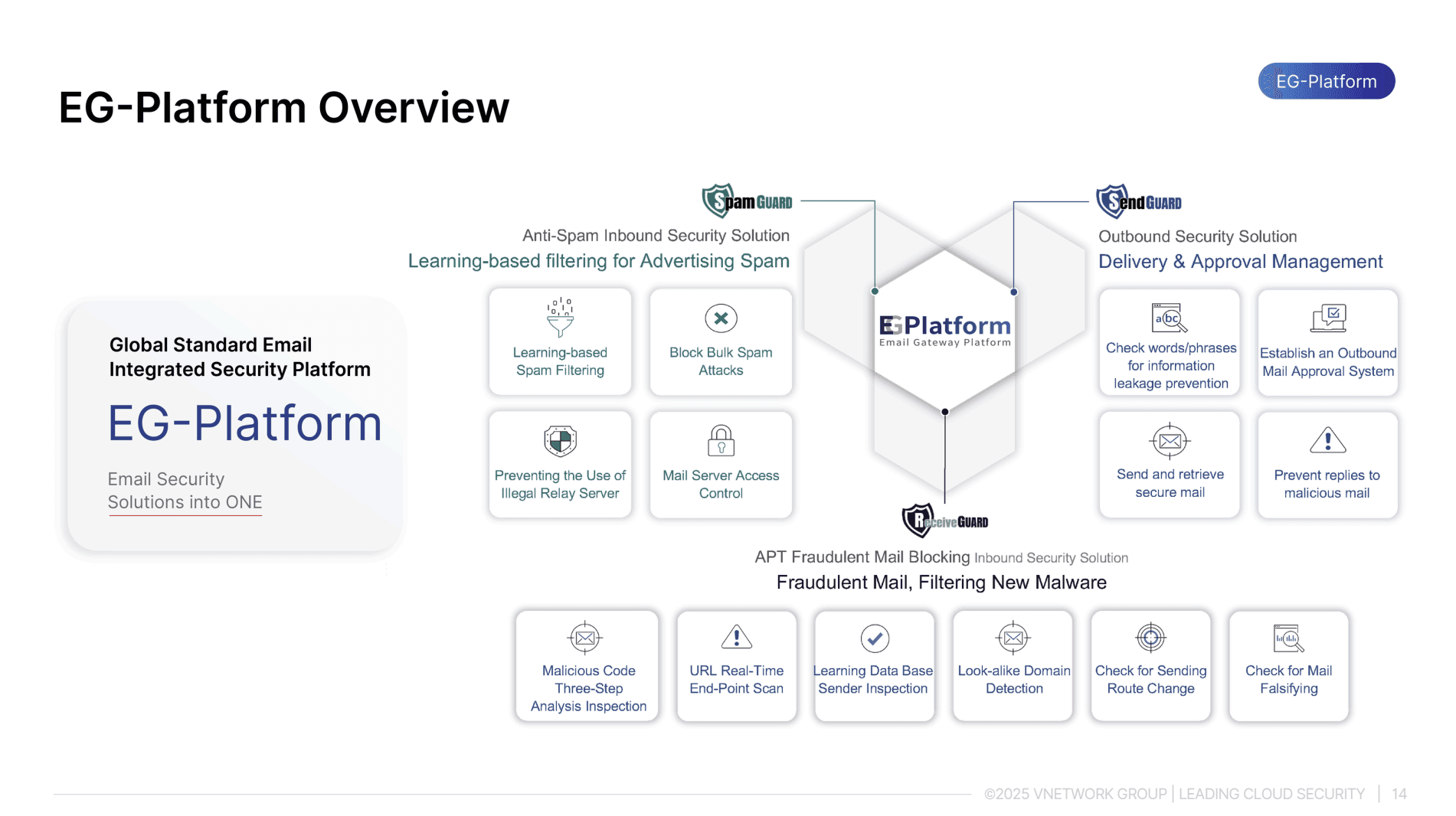
8.2. Key features
- Early detection of sophisticated phishing and scam email campaigns before damage occurs, even when the email contains no malware.
- Sandbox analysis of dangerous attachments and URLs in an isolated environment, responding to zero-day attacks in real time.
- User behavior analysis to identify domain-spoofed emails with high similarity to legitimate addresses that traditional filters would miss.
- Two-way email protection that simultaneously blocks external attacks and prevents internal data leakage via email. Fully integrated with web protection infrastructure including WAF and brute force defenses to create a multi-layered perimeter.
- Compliant with the ITU-T X.1236 international email security standard, meeting the requirements of the Cybersecurity Law and the Personal Data Protection Law.
Conclusion
Scams are an increasingly sophisticated threat targeting both individuals and organizations through diverse channels, from scam emails and social media fraud to complex BEC attacks. Understanding what a scam is, the psychological mechanisms attackers exploit, the warning signs to watch for, and how to build effective prevention processes is the essential first step toward protecting assets and data. Organizations need to combine employee training with technical security systems, and EG-Platform by VNETWORK is a specialized solution for email security and fraud prevention. Contact VNETWORK today for expert guidance on a protection strategy tailored to the scale and industry-specific needs of your organization.
FAQ - Frequently asked questions about scams
1. What is a scam and how does it differ from phishing?
A scam is a term referring to any deliberate act of deception intended to steal a victim's assets, data, or access credentials. Phishing is a specific type of scam focused on impersonating the website or email of a trusted organization to steal login credentials. In other words, phishing is always a scam, but not all scams are phishing.
2. What are the typical characteristics of a scam email?
Scam emails typically feature a sender address that does not match the organization's name, content that creates urgency or presents an unusually attractive offer, requests to click a link or download an attachment, and a failure to address the recipient by name. Carefully checking the email header and the sending domain is the fastest way to verify legitimacy.
3. What should a business do immediately after discovering a scam?
Upon discovering a scam incident, the organization should immediately isolate and contain the affected systems, change all passwords for related accounts, contact the bank if any unusual financial transactions have occurred, and report the matter to the IT department or a security provider to investigate the root cause and prevent recurrence.
4. What does "scam" mean in a financial context?
In a financial context, a scam refers to fraudulent activities designed to steal money from victims through fictitious investments, disguised pyramid schemes, counterfeit trading platforms, or fake digital wallets. Victims are typically lured in by promises of high returns and low risk, while in reality there is no genuine product or business activity behind the scheme.
5. How can scam activity be reported in Vietnam?
In Vietnam, users can report scam activity to the Authority of Information Security under the Ministry of Information and Communications through its official portal, or to local police authorities. Social media platforms and banks also operate dedicated online channels for reporting fraud, enabling timely responses and public awareness campaigns.
