1. What is ransomware?
Ransomware, also referred to as extortion malware, is a type of malware that uses encryption techniques to seize the data of individuals or organizations, then demands that victims pay a ransom to restore access. It is one of the most dangerous cybersecurity threats today, targeting organizations that hold high-value data.
Unlike other forms of cyberattack, ransomware creates direct financial leverage over its victims: either pay the ransom or lose the data permanently. This mechanism is what makes ransomware an extremely effective criminal tool, generating significant profit for attackers at relatively low risk.
On a technical level, ransomware typically uses strong encryption algorithms to lock the victim's files. Decryption is only possible with a secret key controlled by the attacker. This is why prevention and building a web security system early is far more important than attempting to respond after an attack has occurred.
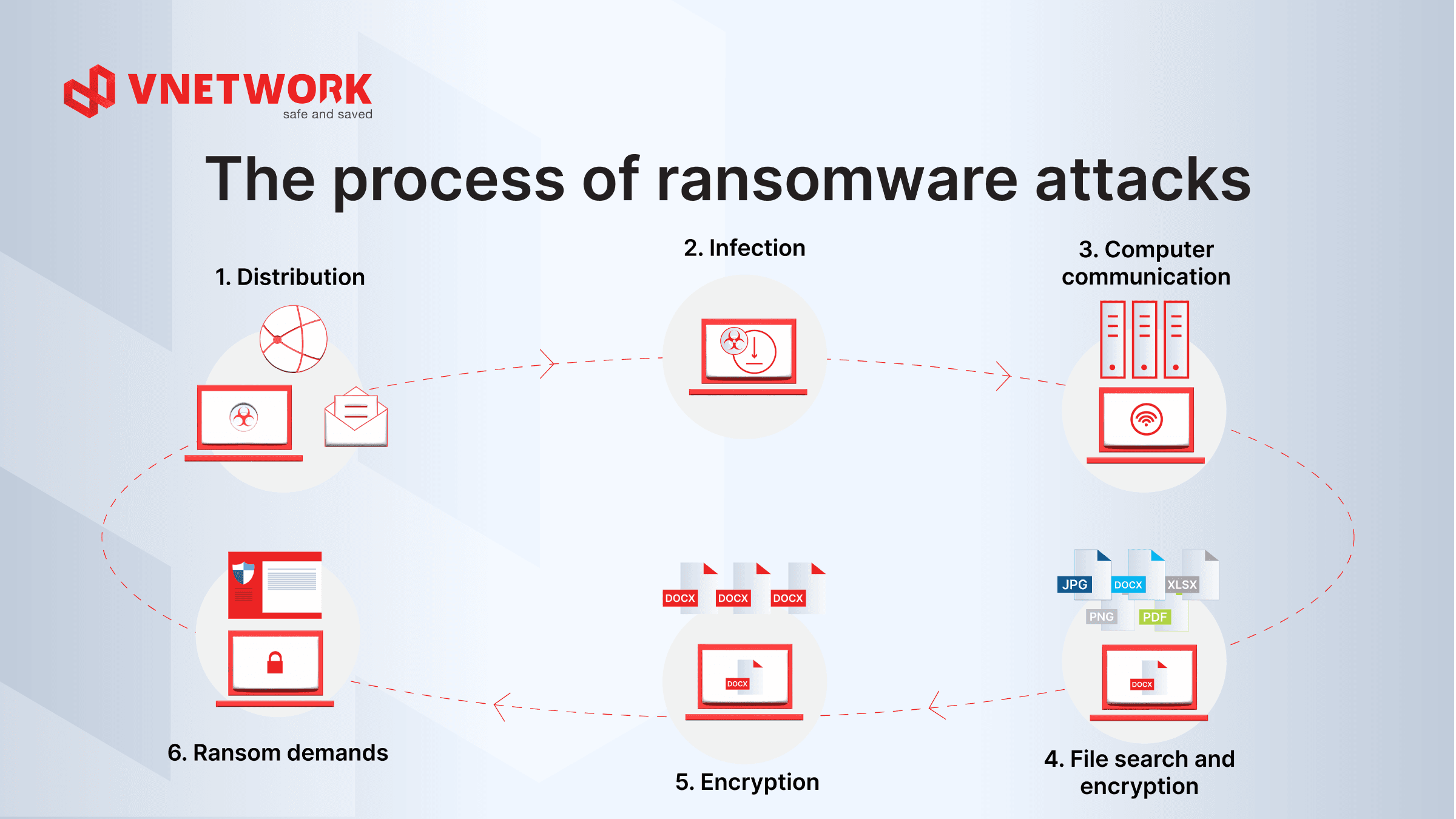
2. How does ransomware work?
To defend effectively, businesses need to understand the attack chain ransomware follows from initial infiltration through to the ransom demand. This process typically unfolds according to a sequential scenario, with each stage presenting control points where security systems can intervene.
- Step 1 - Distribution: Ransomware spreads through multiple vectors, with phishing email being the most common. Attackers send emails containing malicious attachments or links leading to malware-infected pages, exploiting user inattention to trigger the attack. Ransomware can also spread via USB devices, internal network file shares, spam mail, or by directly exploiting vulnerabilities in unpatched software.
- Step 2 - Infection: When a user opens the malicious attachment or clicks the link, ransomware is activated and begins copying executable files into the system. Many modern variants exploit zero-day vulnerabilities or escalate privileges to gain administrative rights, and establish persistence mechanisms to survive system reboots.
- Step 3 - Computer communication: After successfully infecting the system, ransomware establishes a connection to a remote command-and-control server to receive the encryption key and execution instructions. This connection is typically encrypted and routed through anonymizing networks to avoid detection by enterprise firewall and network monitoring systems.
- Step 4 - File search & encryption: Ransomware automatically scans the entire system to catalog high-value files: office documents, databases, images, videos, and especially backup files. The scan typically extends to shared network drives, connected storage devices, and even data synchronized to cloud storage if the system is connected.
- Step 5 - Encryption: After completing the target list, ransomware encrypts all identified files using strong cryptographic algorithms. Encrypted files typically have their extensions changed to unfamiliar formats, rendering the data completely unreadable without the decryption key held by the attacker. The entire process runs silently in the background; users usually do not notice until encryption is complete.
- Step 6 - Ransom demand: Once encryption is complete, ransomware displays a ransom note on the victim's screen, along with a payment deadline and detailed instructions. Ransom payments are almost always demanded in cryptocurrency to avoid tracing. If payment is made, the attacker may provide the decryption key, but there is no guarantee that data will be fully recovered.
Comparison table of the most common infection vectors
| Infection vector | Mechanism | Prevalence | Control point |
| Phishing email | Malicious attachment or link embedded in email | Very high | Email security gateway, security awareness training |
| Software vulnerability | Exploitation of unpatched flaws in OS or applications | High | Patch management, WAF |
| Malicious website | Drive-by download when visiting a compromised site | Medium | Web filtering, endpoint protection |
| USB device | Hidden executable on infected USB activates on connection | Medium | USB policy, endpoint security |
| Network file share | Lateral spread from infected machine to shared drives | Medium | Network segmentation, access control |
| RDP brute force | Password-guessing attack against Remote Desktop Protocol | Growing | MFA, rate limiting, mandatory VPN |
3. The 6 most common ransomware types
Ransomware is not a single type of malware but rather a family of malicious software with many variants, each with its own operating mechanism and level of danger. Understanding each type helps businesses build a defense strategy that targets the right threats.
1. Crypto-ransomware: Encrypts all data
Crypto-ransomware is the most prevalent and also the most dangerous form within the ransomware family. This type focuses entirely on encrypting the victim's data using military-grade encryption algorithms, then demands a ransom in exchange for the decryption key.
Identifying characteristics of crypto-ransomware include: files renamed with unfamiliar extensions, the appearance of README files or ransom notes in directories, and unusually slow computer performance due to the encryption process consuming system resources. This ransomware type typically targets entire drives, including folders synchronized with cloud storage and shared network drives.
The consequences of a crypto-ransomware attack are severe because even if the victim pays the ransom, there is no guarantee that the data will be fully recovered. This is why a 3-2-1 backup strategy and a multi-layered Web/App/API security solution are indispensable foundations of any defense posture.
2. Leakware (doxware): Steal and threaten to publish data
Leakware, also known as doxware or exfiltrationware, is a dangerous ransomware variant that executes a double-extortion scheme. In addition to encrypting data, leakware steals sensitive information before encryption and threatens to publish it publicly if the victim refuses to pay.
Leakware is especially dangerous for businesses that hold customer information, trade secrets, or sensitive financial data. Even if the business has solid backups and does not need to pay to restore data, the threat of public exposure still forces many organizations to meet the attacker's demands. This is also a leading cause of serious data breaches, triggering legal liability under the Personal Data Protection Law.
3. Scareware: Psychological attack on users
Scareware is a ransomware type that exploits users' fears and lack of knowledge to commit fraud. Rather than actually encrypting data, scareware displays fake security warnings or alerts about nonexistent system problems, convincing victims to pay to "resolve" the issue. This attack type is commonly distributed through fraudulent emails or malicious web advertisements.
Scareware operates in three consecutive stages: impersonating the interface of a reputable security product to create a false sense of trust, displaying continuous warnings about viruses or critical system threats to cause panic, then directing users to purchase or install the promoted software to fix the problem. That software may itself contain additional malware or simply be a useless product.
4. Ransomware-as-a-Service (RaaS): The criminal service model
RaaS is a cybercriminal business model that operates like a cloud service: professional hacker groups develop ransomware and lease it on the dark web, allowing anyone, including those with no technical skills, to carry out ransomware attacks. This is a primary reason for the sharp increase in ransomware attacks in recent years.
The RaaS ecosystem consists of ransomware developers who provide tools and infrastructure, affiliates who rent those tools and execute attacks, and a revenue-sharing arrangement based on an agreed split of the ransom collected. This model even comes with customer support services, campaign management dashboards, and in some cases service-level agreements covering response times.
The risk from RaaS is significant because it lowers the technical barrier for cybercriminals. To counter this model, businesses need to build a multi-layered defense system that combines WAF, continuous monitoring, and security awareness training for all staff.
5. DDoS ransomware (Ransom DDoS): Extortion through denial-of-service attacks
DDoS Ransomware, also known as Ransom DDoS, is a ransomware variant that does not encrypt files. Instead, it carries out or threatens to carry out a large-scale DDoS attack against the victim's infrastructure if a ransom is not paid. This form of extortion requires no intrusion into the victim's internal systems, making it difficult to prevent through conventional means.
Attackers typically begin with a small-scale test DDoS attack to demonstrate their capability, then send a threat warning of a much larger attack unless a ransom is received within a set deadline. This method is particularly dangerous for businesses that depend on online services such as e-commerce, finance, gaming, or streaming. To defend against this type of attack, businesses need to deploy a dedicated anti-DDoS solution capable of handling large traffic volumes and detecting early attack indicators.
6. Wiper ransomware: total destruction with no ransom
Wiper Ransomware is the most dangerous variant in the ransomware family because its goal is not ransom collection but outright destruction. This malware permanently deletes or overwrites data, making recovery impossible even if the victim is willing to pay any amount. Wipers are often disguised as ransomware to create confusion and misdirect the victim's response.
Wiper Ransomware is typically deployed in attacks with political, cyber-espionage, or economic sabotage motivations. Priority targets are critical infrastructure: power, water, finance, healthcare, and government systems. No rootkit or advanced stealth technique can reliably detect a wiper before it is too late, making proactive defense and regular offline backups the only sufficiently effective countermeasures.
4. Comparison table: the 6 ransomware types by severity
| Type | Target | Primary mechanism | Impact | Recoverability |
| Crypto-ransomware | Business data | File encryption via strong algorithm | Complete loss of data access | Feasible with clean backup |
| Leakware (Doxware) | Sensitive data | Data exfiltration before encryption | Data loss, secret exposure, legal liability | Technical recovery possible; exfiltrated data cannot be recalled |
| Scareware | Individuals, SMEs | Fake security alerts exploiting fear | Financial loss, additional malware installed | High if detected early |
| RaaS | Any target | Hired attack via service model | Varies by ransomware variant used | Depends on ransomware type employed |
| DDoS ransomware | Online services | Traffic flood disables services | Service disruption, revenue loss | High once attack stops |
| Wiper ransomware | Critical infrastructure | Permanent data deletion or overwrite | Irreversible system destruction | Very low; entirely dependent on offline backup |
5. Consequences of a ransomware attack on a business
A successful ransomware attack does not only cause immediate damage; it leaves lasting consequences across multiple dimensions. Businesses need to fully appreciate the scope of the impact to understand the true importance of investing in security.
Data loss and business disruption
The most direct and immediate impact is the loss of access to critical data: internal documents, customer information, financial records, HR files, and entire operational databases. When core systems are paralyzed, all business activities must halt. Recovery time following a serious ransomware attack can range from several days to several weeks, depending on the size of the organization and the readiness of its data backup systems.
Financial damage and reputational harm
The true cost of a ransomware attack is typically far greater than the demanded ransom amount. Businesses must absorb multiple overlapping expenses: the ransom itself (if paid), system recovery costs and cybersecurity consultant fees, revenue lost during the downtime period, incident notification costs to customers and partners, and the cost of upgrading security systems after the incident.
On the reputational side, a serious security incident erodes customer trust, especially when information about the attack becomes public. Rebuilding brand reputation often takes months to years and requires significant investment in crisis communications and security certifications such as ISO 27001.
Legal and compliance risk (Personal Data Protection Law, Cybersecurity Law)
The legal framework for data security in Vietnam is tightening. The Personal Data Protection Law and the Cybersecurity Law impose clear obligations for data protection and incident reporting. Businesses that experience a ransomware-related data leak may face administrative penalties, compensation claims from affected parties, and mandatory oversight from regulatory authorities.
Additionally, if the business provides services to international partners, a data breach may trigger legal liability under foreign regulations, particularly for organizations involved in digital transformation and cross-border data processing.
6. A ransomware protection checklist for businesses
No single solution is sufficient to fully prevent ransomware. An effective defense strategy requires combining multiple layers of protection following a Defense-in-Depth model.
Group 1: Technical measures (WAF, firewall, backup, patching)
The technical protection layer is the foundation of any anti-ransomware strategy. Businesses must deploy all of the following components:
- Network firewall: tightly configured to block unauthorized connections from outside the internal network
- WAF (Web Application Firewall): protects web applications and APIs from common attack vectors such as SQL Injection, XSS, and vulnerabilities in the OWASP Top 10
- Patch management: establish automated security update processes and prioritize patching critical vulnerabilities within 48 to 72 hours of release
- 3-2-1 backup rule: 3 copies on 2 different storage media, with 1 copy stored offline or air-gapped to prevent encryption by ransomware
- Endpoint Detection and Response (EDR): monitor for abnormal activity on endpoints and respond automatically when suspicious behavior is detected
- Email protection using spam filtering and malicious attachment detection before messages reach user inboxes
Group 2: Access control and privilege management (Zero Trust)
The Zero Trust model, based on the principle of "never trust by default, always verify," is the most suitable security framework for combating modern ransomware. Key principles to implement include:
- Principle of Least Privilege: each user and process should only have access to the resources strictly necessary for their work
- Multi-factor authentication (MFA): mandatory for all administrator accounts and broadly applied to employees, especially for remote access. MFA effectively prevents brute force attacks against user accounts
- Network segmentation: divide the internal network into separate zones to limit the spread of ransomware when one device is infected
- Privileged account activity monitoring: track and alert on any abnormal activity from system administrator accounts
Group 3: Staff training and incident response procedures
The human element remains the biggest vulnerability in the security chain. Attackers frequently use social engineering techniques to bypass even the most sophisticated technical controls. A security training program should include:
- Recognizing phishing, spear phishing, and indicators of fraudulent emails and email spoofing
- Clear incident reporting procedures: who to contact immediately when an anomaly is detected, and how to isolate a suspected infected device
- Regular incident response exercises (tabletop exercises): simulate ransomware attack scenarios so employees know exactly what to do when an incident occurs
- Business continuity and disaster recovery plan (BCP/DRP): fully document system recovery procedures in priority order to minimize downtime
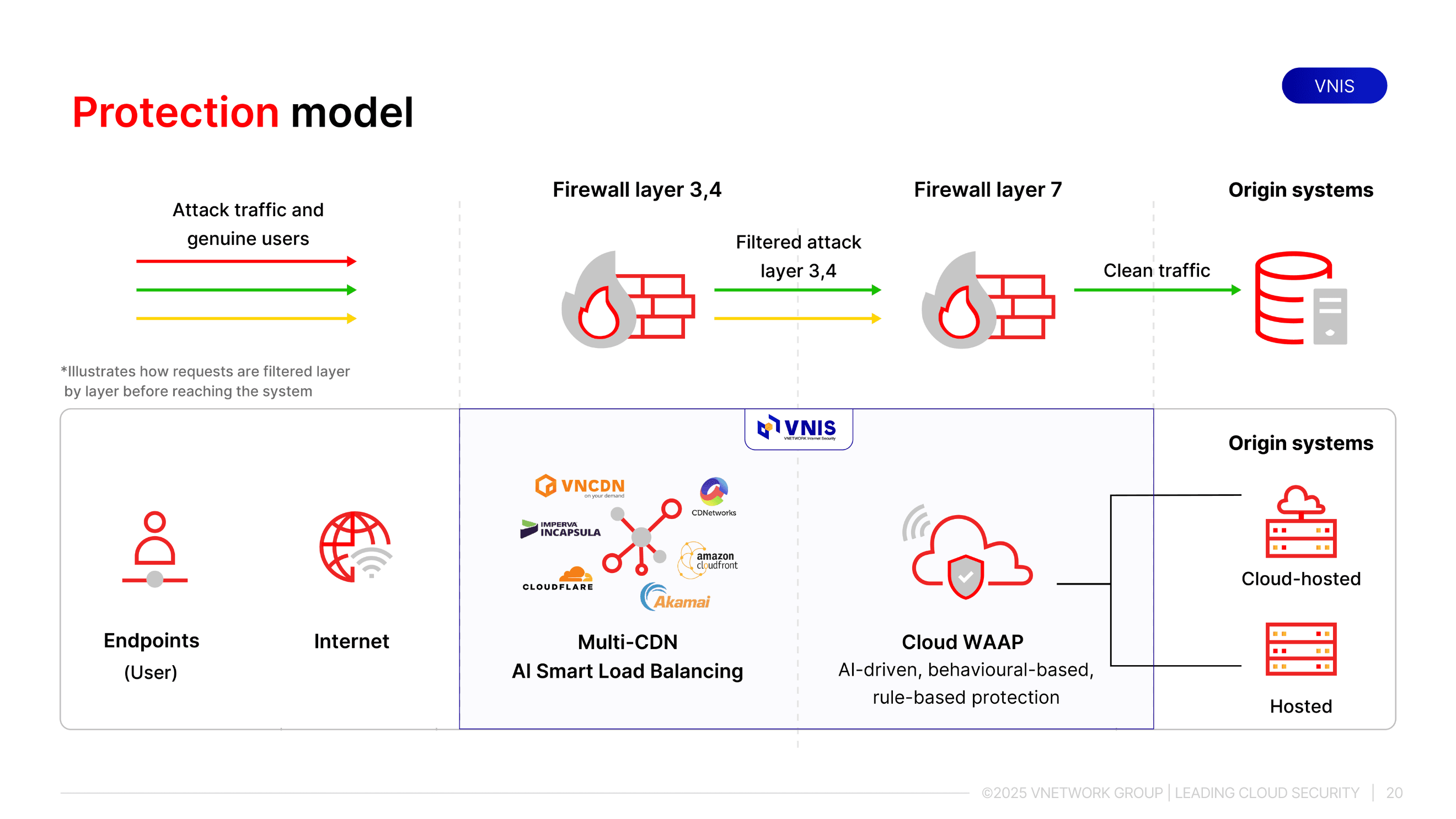
7. VNIS: comprehensive protection against all ransomware variants
VNIS (VNETWORK Internet Security) is VNETWORK's Web/App/API security and acceleration platform, designed to help businesses proactively defend against cybersecurity threats. The system provides real-time protection against multi-layer DDoS attacks (Layer 3/4/7), malicious bots, security vulnerabilities such as SQL Injection, XSS, zero-day exploits, malware, and dangerous crawlers. VNIS applies AI to detect and block abnormal behavior at an early stage while maintaining performance and user experience.
- Layer 1: VNIS combines AI Smart Load Balancing and Multi-CDN to handle network-layer DDoS attacks. AI automatically analyzes access behavior, distributes traffic intelligently, and eliminates abnormal traffic sources before they overwhelm the system. As a result, the business's website and applications remain stable even during peak attack periods.
- Layer 2: VNIS deploys WAAP (Web Application and API Protection) powered by AI to block Layer 7 DDoS, malicious bots, and common security vulnerabilities from the OWASP Top 10 list. This layer directly protects the processing logic of web applications and APIs, which are often the most deeply exploited and the hardest to detect using conventional defenses.
The 24/7/365 monitoring system automatically sends early alerts when attack indicators are detected. Notably, VNETWORK's dedicated SOC team operates continuously across Vietnam, Hong Kong, Taiwan, Singapore, and the United Kingdom, ready to engage alongside businesses in any emergency to minimize losses.
8. EG-Platform: blocking ransomware at the email gateway
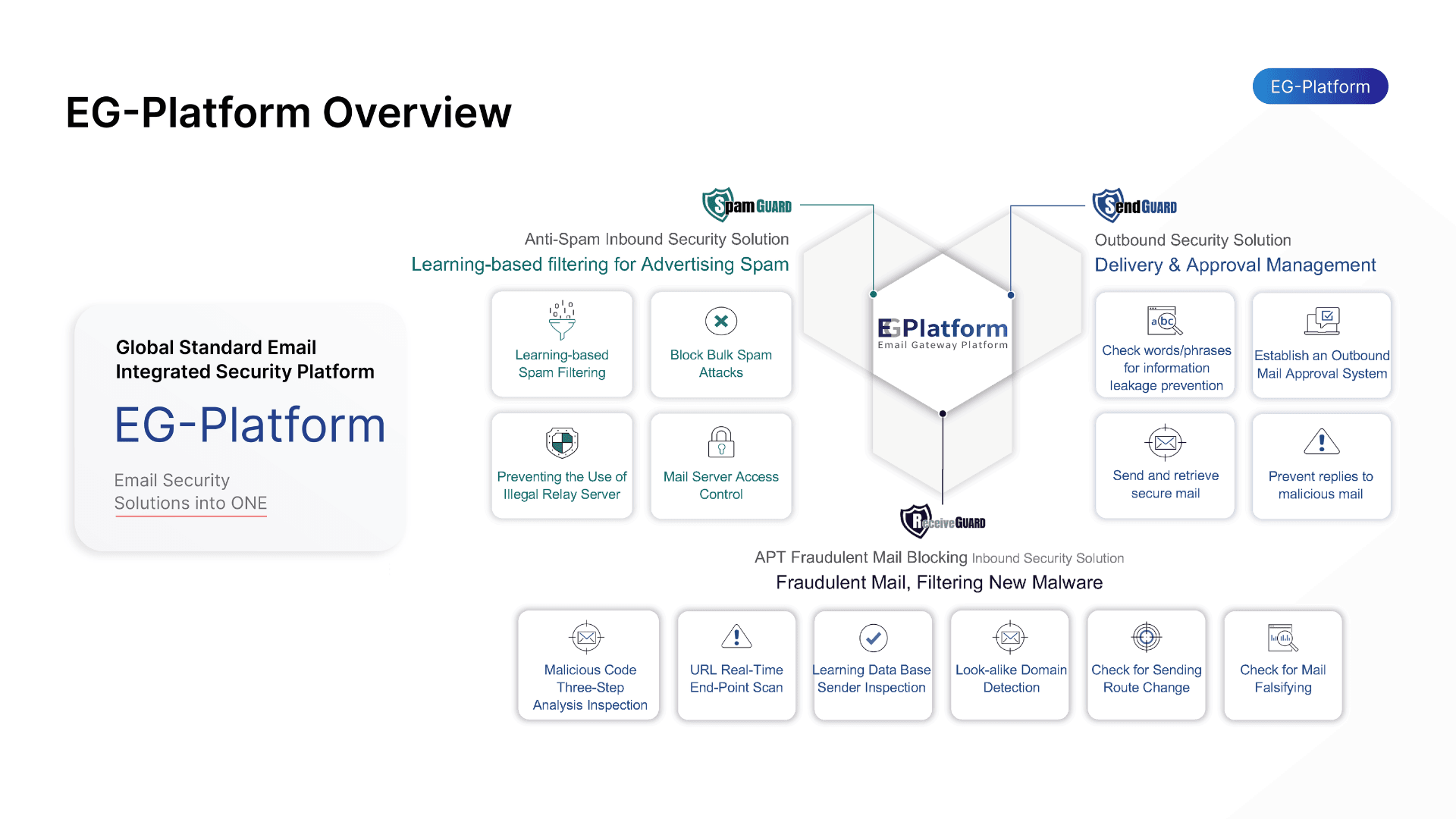
The majority of ransomware attacks begin with a malicious email. VNETWORK's EG-Platform is an AI and machine learning-powered email security platform that provides comprehensive two-way email protection (both inbound and outbound), blocking phishing, social engineering, and targeted email attacks before malware reaches the user. In particular, EG-Platform is an email security platform that meets the ITU-T X.1236 standard set by the International Telecommunication Union.
EG-Platform operates through a three-layer independent protection model:
- Spam Guard uses Machine Learning and a Bayesian filter to score the risk of each email, verifying SPF, DKIM, and DMARC authentication standards to detect domain spoofing. This layer filters and blocks spam, phishing mail, and malware-carrying emails before they reach users' inboxes.
- Receive Guard protects inbound email by inspecting all content, attachments, and URLs within a virtualized sandbox environment. The system analyzes IPs, headers, and anomalous behavior to identify fraudulent emails. When a risk is detected, suspicious links are disabled immediately before the user has a chance to access them.
- Send Guard controls outbound email, preventing compromised internal accounts from distributing spear phishing or leaking data externally. Filtering by IP, country, and sensitive content minimizes the risk of an incident spreading beyond the organization.
9. Conclusion
Ransomware is no longer a threat that can be ignored or addressed reactively. With the emergence of sophisticated criminal models such as RaaS and destructive variants like Wiper Ransomware, businesses of all sizes need to proactively build a comprehensive defense strategy that combines technical solutions, strict security policies, and ongoing staff training.
VNETWORK's VNIS platform is designed to protect businesses against all forms of cyberattack, including every common ransomware type. With its global infrastructure, advanced AI technology, and dedicated SOC team, VNIS serves as the last line of defense, enabling businesses to maintain continuous operations even in the face of highly sophisticated attacks.
Contact VNETWORK today for security solution recommendations tailored to your business size and industry: Hotline +84 (028) 7306 8789 or email contact@vnetwork.vn.
10. FAQ — Frequently asked questions about ransomware
1. What is ransomware and how does it differ from regular malware?
Ransomware is a specialized type of malware that encrypts a victim's data and demands a ransom in exchange for the decryption key. The core distinction from regular malware is that ransomware creates direct financial leverage rather than simply causing damage or silently stealing data. This is also what makes ransomware especially dangerous for businesses: it forces the organization into a stark choice between paying the ransom and losing data permanently.
2. Can ransomware be completely prevented?
No solution guarantees 100% ransomware prevention, as attackers continuously develop new variants. However, a multi-layered defense strategy incorporating WAF, patch management, MFA, network segmentation, and staff training can significantly reduce the probability of a successful attack. More importantly, a strong backup plan enables businesses to recover quickly without paying a ransom even when an attack occurs.
3. Should a business pay the ransom after a ransomware attack?
Authorities and security experts universally advise against paying the ransom for several reasons: there is no guarantee data will be recovered after payment; paying sustains the criminal ecosystem and makes the business a likely target for a second attack; and some countries may treat paying a ransom to sanctioned groups as a violation of law. Instead, businesses should focus on restoring from clean backups and reporting the incident to the relevant authorities.
4. What is the difference between DDoS ransomware and Ransom DDoS?
DDoS Ransomware and Ransom DDoS are in fact two names for the same type of attack: the attacker carries out or threatens to carry out a distributed denial-of-service attack to extort the victim, rather than encrypting data like traditional ransomware. This is a form of extortion that requires no intrusion into the victim's internal systems and instead targets the accessibility of the business's online services.
5. Can a WAF protect a business from ransomware?
A WAF (Web Application Firewall) helps block many of the attack vectors ransomware commonly exploits to infiltrate systems, particularly through web application vulnerabilities. However, a WAF is only one layer within a multi-layered defense system and must be combined with endpoint security, email filtering, patch management, and a backup plan to provide comprehensive protection against ransomware.
6. Do small businesses need to worry about ransomware?
Yes. Small businesses are actually preferred targets for many attack groups because they tend to have more limited security resources while still holding valuable data. The growth of the RaaS (Ransomware-as-a-Service) model makes it easy for attackers to target many small organizations simultaneously rather than focusing exclusively on large enterprises. Businesses of all sizes need to build a basic security strategy.
